パスキー
よりシンプルで強力なパスワードレス・サインインの利用を加速する
パスキー
/ˈpasˌkēs/
名詞
FIDO標準に基づき、パスキーはパスワードに代わるもので、ユーザーのデバイスにまたがるウェブサイトやアプリへのサインインをより迅速、簡単、かつ安全に行うことができる。 パスワードとは異なり、パスキーは常に強固でフィッシングに強い。
パスキーは、アプリやウェブサイトのアカウント登録を簡素化し、使いやすく、ユーザーのほとんどのデバイスで機能し、物理的に近くにある他のデバイスでも機能する。
なぜパスキーなのか?
パスワードは問題だ。
*HYPR、2022年パスワードレス・セキュリティ・レポート – レポートのダウンロードはこちら。
レガシー認証ソリューションは、セキュリティの問題に対処していない、あるいは、大規模な消費者の利用には十分に使えない。

Fido認証は、パスワード問題に対する世界の答えである。
FIDO認証は、フィッシングに強いセキュリティで、よりシンプルなユーザーエクスペリエンスを提供します。
パスキーがFIDO認証のアクセスとユーザビリティを最適化する
組織は様々なユースケースにおいて、パスキーによるFIDOサインインを導入することができる。 パスキーは、ユーザがすべてのアカウントですべてのデバイスを再登録することなく、新しいデバイスであっても多くのデバイスでFIDOサインイン認証情報にアクセスすることを可能にする。 あるいは、FIDOセキュリティキーまたはプラットフォームにバインドされたデバイス固定パスキーは、同期を必要としない組織のためのオプションである。
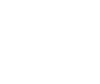
ユーザーはパスキーをどのように使うのか?
ユーザーがアプリやウェブサイトへのサインインを求められると、ユーザーはデバイス(電話、コンピューター、セキュリティキー)のロックを解除するのと同じバイオメトリクスやPINでサインインを承認する。 アプリやウェブサイトは、従来の(そして安全でない)ユーザー名とパスワードの代わりに、この仕組みを使うことができる。
これが意味するものは…

ユーザー・エクスペリエンス
ユーザーエクスペリエンスは、ユーザーの多くのデバイスで使い慣れた一貫性のあるものになる。指紋や顔、またはデバイスの暗証番号の単純な認証であり、消費者がデバイスのロックを解除するために毎日何度も行っているのと同じ単純な操作である。

セキュリティ
パスキーはFIDO認証に基づいており、フィッシング、クレデンシャル・スタッフィング、その他の遠隔攻撃の脅威に対する耐性が証明されています。 また、サービス・プロバイダーは、サインインやアカウント回復の代替手段として、パスワードを必要としないパスキーを提供することができる。

スケーラビリティ
パスキーを使えば、ユーザーは各サービスや各新規デバイスで新しいFIDOクレデンシャルを登録する必要がない(通常、最初のサインインにはパスワードが必要になる)。 ユーザーのパスキーは、デバイスを交換しても、必要なときにいつでも利用できる。 同期をサポートしないデバイス・バインド・パスキーは、ユーザーのパスキーの証明証明を追加で必要とする組織のためのオプションです。

パスキー・ロゴ
パスワードの代わりにパスキーを使用できるサイトでは、パスキーのロゴを探してください。 このロゴの使用を希望されるサービスプロバイダーは、FIDO Trademark and Service Mark Usage Agreement for Websitesをご覧いただき、条件に同意の上、ロゴファイルをダウンロードしてください。
passkeyロゴスタイルガイドファイルのダウンロード
リソース
開発者向けリソース
準備はできたか?
アップルとグーグルは、開発者向けにこれらのパスキーリソースを作成した:
ビデオ
パスキーの活躍
プラットフォーム間のパスキーのデモ。
パスキー入門
パスキーの徹底解説。