Companion Programs are independent testing programs that FIDO partners use to lessen the certification burden on vendors. Companion Programs can be found within Security Level 3 and Level 3+.
The vendor is given access to a document prepared by FIDO Alliance’s Security Requirements Working Group to aid in completing L3 or L3+ Certification and the Mapping Table. The table maps requirements from the Companion Program to the FIDO Security and Privacy Requirements.
The FIDO Authenticator Certification Companion Program typically covers the underlying platform, which provides security functionalities to the Authenticator Application. The goal is to ensure that the security policy of the FIDO Authenticator does not contradict the security policy of the underlying platform (e.g. IC + Java Card OS) and that the final product (IC + OS + FIDO Authenticator) fulfills the FIDO Security Requirements as defined for L3 and L3+.
The vendor should complete this mapping table by referencing their Partner Program evidence or add new evidence to fulfill all FIDO security requirements relevant to the Target of Evaluation. Applying for high-level certification without a Companion Program is not recommended.
To ensure the Companion Program is included, follow these 3 steps:
- Formulate a Security Target (ST) for the Authenticator Application independently from the underlying platform.
- Use the mapping spreadsheet to identify the intersection between the ST of the Authenticator Application and the certified Platform ST. Analyze and compare g their security functionality and complete this table by adding a column called “coverage rationale”.
- Identify under which conditions the application can trust and rely on the certified platform security functionality used by the composite TOE without re-evaluating the conditions and provide a justification.
- Determine the certification level desired and submit the Companion Program evidence to a FIDO Accredited Lab.
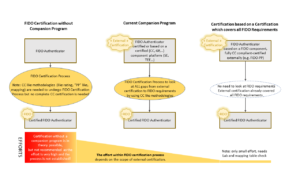
The following figure describes the workload and the scenarios to achieve FIDO L3/L3+ certification.
Current Approved FIDO Authenticator Certification Companion Programs:
Common Criteria Companion ProgramsCommon Criteria or ISO/IEC 15408, with Protection Profiles covering Secure Elements (SE), i.e. Smart Cards and other form factors, claiming an AVA_VAN.3 (or higher) vulnerability assessment. This includes: |
Global Platform Companion ProgramGlobalPlatform TEE, claiming an AVA_VAN_.AP3 vulnerability assessment, with TEE PP. |
Certification Companion Programs for Future Development:
|
FIDO welcomes industry experts and their contributions toward the development of these programs. Please email the Certification Secretariat, if you are interested in contributing.

