The FIDO Alliance has published three sets of specifications for simpler, stronger user authentication: FIDO Universal Second Factor (FIDO U2F), FIDO Universal Authentication Framework (FIDO UAF) and the Client to Authenticator Protocols (CTAP). CTAP is complementary to the W3C’s Web Authentication (WebAuthn) specification; together, they are known as FIDO2.
FIDO standards use standard public key cryptography techniques to provide phishing-resistant authentication with cryptographic key pairs called passkeys. FIDO is designed from the ground up to protect user privacy and prevent phishing. Every passkey is unique and bound to the online service domain. The protocols do not provide information that can be used by different online services to collaborate and track a user across the services. Biometric information, if used, never leaves the user’s device.
Read the technical specifications on the specifications download page.In addition to meeting the technical requirements, the FIDO Alliance developed further security requirements that need to be implemented to enhance the security assurance of each device. These requirements are covered in the Authenticator Certification program found on the Certified Authenticator Levels page.
FIDO2
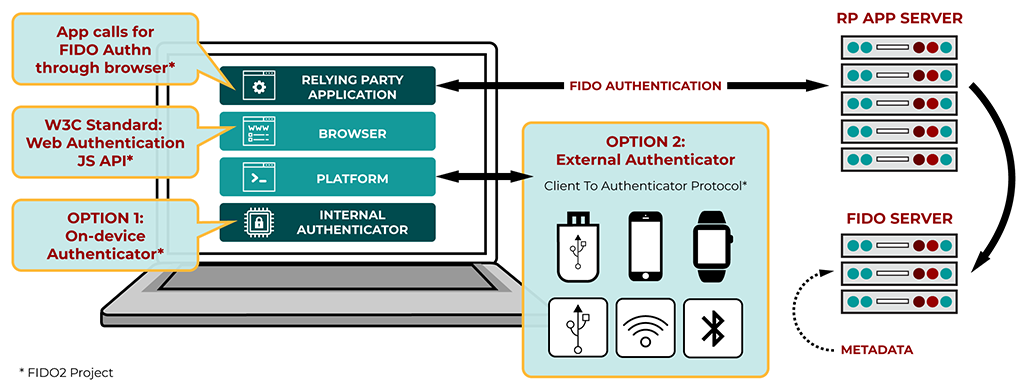
FIDO2 is comprised of the W3C Web Authentication specification and corresponding Client-to-Authenticator Protocols (CTAP) from the FIDO Alliance. FIDO2 supports passwordless, second-factor and multi-factor user experiences with embedded (or bound) authenticators (such as biometrics or PINs) or external (or roaming) authenticators (such as FIDO Security Keys, mobile devices, wearables, etc.).
The specifications within FIDO2 are:
W3C WebAuthn
WebAuthn defines a standard web API that is being built into browsers and platforms to enable support for FIDO Authentication.
CTAP2
CTAP2 allows the use of external authenticators (FIDO Security Keys, mobile devices) for authentication on FIDO2-enabled browsers and operating systems over USB, NFC, or BLE for a passwordless, second-factor or multi-factor authentication experience.
CTAP1
The new name for FIDO U2F, CTAP1 allows the use of existing FIDO U2F devices (such as FIDO Security Keys) for authentication on FIDO2-enabled browsers and operating systems over USB, NFC, or BLE for a second-factor experience.
FIDO UAF
FIDO UAF supports a passwordless experience. WIth FIDO UAF, the user carries a device with a FIDO UAF stack installed. They can then register their device to the online service by selecting a local authentication mechanism such as swiping a finger, looking at the camera, speaking into the mic, entering a PIN, etc. The FIDO UAF protocol allows the service to select which mechanisms are presented to the user.
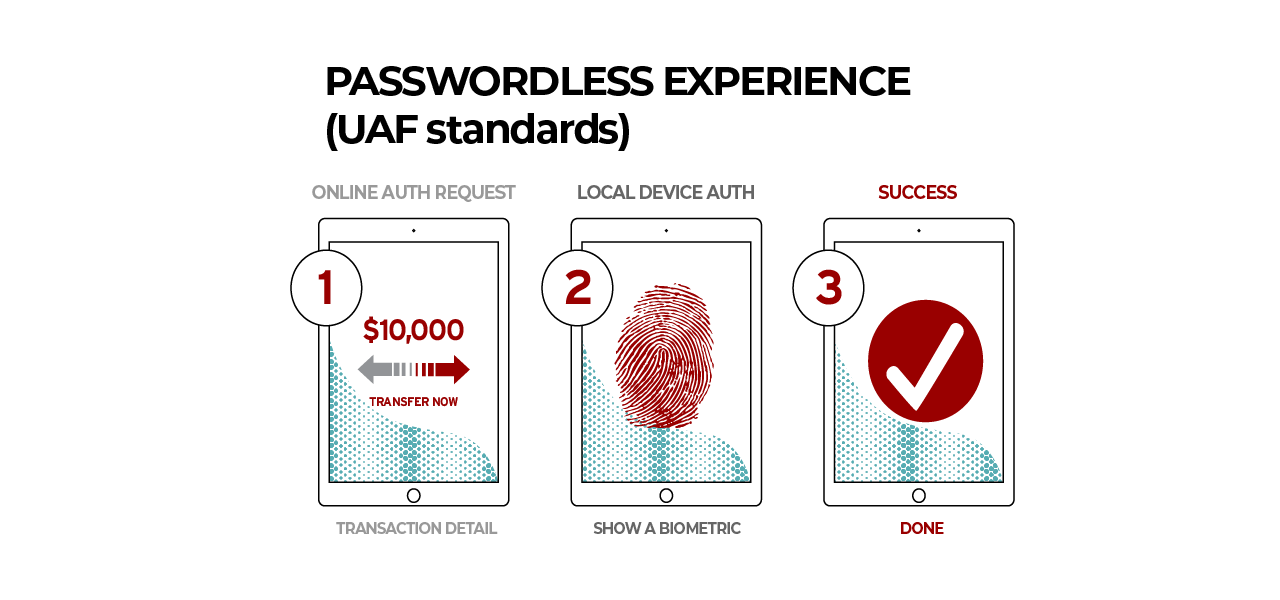
Once registered, the user simply repeats the local authentication action whenever they need to authenticate to the service. The user no longer needs to enter their password when authenticating from that device. FIDO UAF also allows experiences that combine multiple authentication mechanisms such as fingerprint + PIN.
FIDO U2F
FIDO U2F supports a second-factor experience. FIDO U2F allows online services to augment the security of their existing password infrastructure by adding a strong second factor to user login. The user logs in with a username and password as before. The service can also prompt the user to present a second factor device (such as a FIDO Security Key) at any time it chooses. The strong second factor allows the service to simplify its passwords (e.g. 4–digit PIN) without compromising security.

During registration and authentication, the user presents the second factor by simply pressing a button on a USB device or tapping over NFC or BLE. The user can use their FIDO U2F device across all online services that support the protocol leveraging built–in support in web browsers.
With the release of FIDO2, U2F has been relabeled as CTAP1.

