FIDO 安全密钥用户体验指南
我们希望得到您的反馈
如果您是部署FIDO或向市场投放FIDO产品的服务提供商,我们希望听到您的意见,并就您的FIDO经验、这些《FIDO用户体验指南》和/或您想分享的任何其他内容获得您的反馈。
请通过info@fidoalliance.org与我们联系
文件目的
本文档以受监管行业(如银行业或医疗保健业)的使用案例为基础,为依赖方和实施方提供了用户体验(UX)指南和最佳实践,帮助他们使用 FIDO 安全密钥作为第二要素启用多要素身份验证(MFA)。 这些指南旨在加快 FIDO 实施过程中的决策,并明确规定应向用户提供哪些信息和控制措施。 请注意,这些用户体验建议是针对在台式机/笔记本电脑上访问的基于浏览器的网站而优化的,而不是移动应用程序或移动网络。 不过,该指南并不包括有关安全策略或账户恢复的建议。
本文件中的原则是由Blink与FIDO用户体验工作组的成员合作,经过多次(68次)有主持人和无主持人的消费者调研后制定的。 用户研究参与者包括拥有和使用安全密钥(主要用于工作)的消费者,以及潜在的安全密钥用户,他们在个人网上银行中使用双因素身份验证,但在研究之前没有使用安全密钥的经验。 请注意,我们的研究范围不包括吸引潜在用户购买密钥的策略。 除了用户研究之外,FIDO用户体验工作组还对目前市场上主要的第二要素身份验证安全体验进行了审查,并在研究和评估过程中提出了意见和建议。
这些建议代表了FIDO Alliance用户体验工作组就如何在台式机/笔记本电脑上将FIDO安全密钥作为第二要素实施MFA所提出的观点。 在本文件中,”专业消费者 “是指在个人生活中较早采用安全和隐私技术和服务的具有安全和隐私意识的消费者。
这些指南应与FIDO的其他出版物一起使用,如FIDO的标识使用指南、FIDO隐私原则、使残疾用户无障碍使用FIDO部署指南(将于2022年夏季发布)、FIDO桌面验证器用户体验指南以及其他技术文档。 反映本文件指导的实时参考实施情况可在https://digitalbank-test.com上找到。
设备、操作系统和浏览器对 FIDO 的支持会随着时间的推移而变化。 如果您在实施 FIDO 安全密钥验证过程中遇到困难,请考虑使用FIDO-dev 邮件列表等在线资源,或直接通过电子邮件与FIDO Alliance联系。
预期受众
目标受众是任何负责利用 FIDO 安全密钥部署 MFA 的界面或用户体验元素的人员,注意这些指南是基于受监管的行业用例。 受众包括但不限于用户体验设计师、产品经理和软件开发团队。
关于FIDO Alliance和FIDO用户体验工作组
FIDO(快速身份在线)联盟(www.fidoalliance.org)是一个开放的行业协会,其使命是:制定身份验证标准,帮助减少全世界对密码的过度依赖。
FIDO Alliance致力于通过开放标准改变身份验证的本质,提供比密码和 SMS OTPS 更安全、更易于消费者使用、更易于服务提供商部署和管理的登录体验。 在对在线服务进行身份验证时,FIDO 身份验证更强大、更私密、更易用。
该联盟由企业、支付、电信、政府和医疗保健领域的数百位全球技术领袖推动,他们共同支持该组织的使命,即减少全球对密码的依赖。 联盟成员通过影响FIDO规范的制定、建立部署FIDO身份验证的最佳实践,以及提高全球对联盟、联盟使命和FIDO规范的认识,为实现这一使命做出贡献。
FIDOFIDO Alliance董事会为该项目成立了FIDO用户体验特别工作组,以应对挑战并开发最佳用户体验实践,从而在消费者网站的台式机/笔记本电脑跨平台上使用FIDO安全密钥实施MFA。 该项目的成员志愿者包括来自 Feitan、Google、IBM、Idemia、摩根大通银行、Meta、微软、NIST、OneSpan North America、Onfido、Trusona、Trustkey、Visa、VMware 和 Yubico 的产品负责人。 该指南旨在帮助注册人员为消费者安全关键受众设计更好、更一致的用户体验,并最终最大限度地提高采用率。
为什么选择 FIDO?
互联网和移动技术彻底改变了我们的通信、交易和服务方式。 但是,这些进步也带来了一个问题–过度依赖令人沮丧且有风险的密码来验证在线服务用户的身份。
2012年,几个思想领先的组织和个人联合成立了FIDO Alliance。 该联盟的使命是为更简单、更强大的现代身份验证方法制定标准,并促进其广泛采用。 FIDO Alliance取得的一些成功包括
- 已发布基于公钥加密技术的防网络钓鱼、强身份验证标准
- 与万维网联盟(W3C)合作,将 FIDO 技术确立为官方网络标准,该标准现已内置于领先的数十亿设备浏览器和平台中
- 建立认证工具、流程和全球研讨会,促进解决方案开发和互操作性测试
- 全球许多领先的消费电子产品制造商和网络服务品牌都认可了基于 FIDO 标准的方法
鉴于这些成功经验以及全球对FIDO身份验证的日益认可,标有FIDO标识的产品和服务都与防网络钓鱼、可互操作和用户友好的身份验证联系在一起。
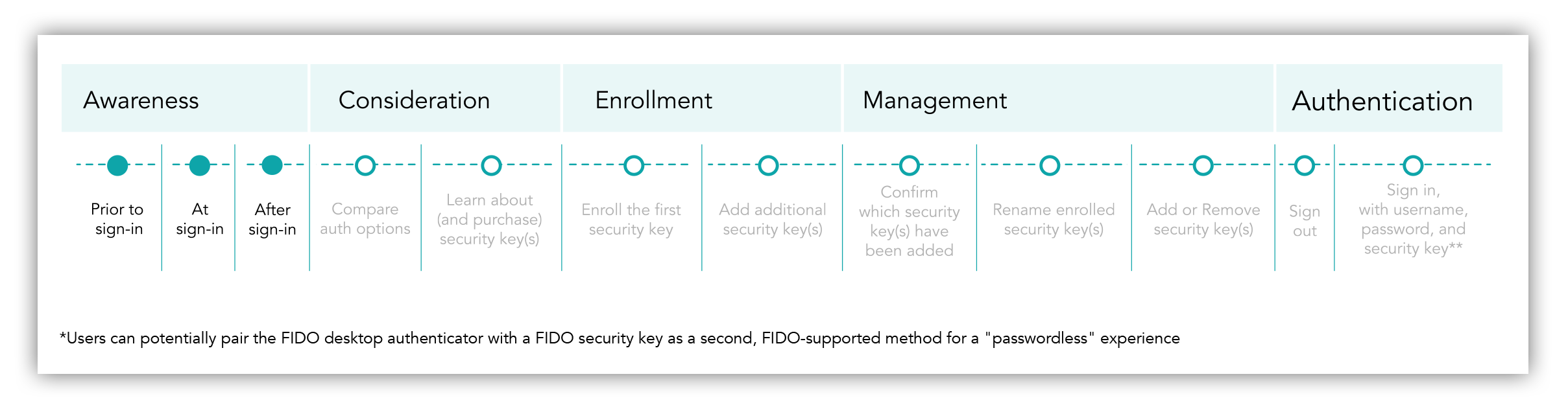
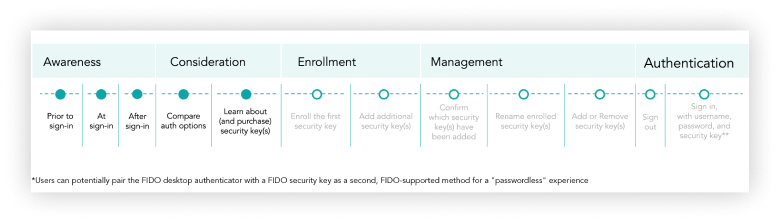
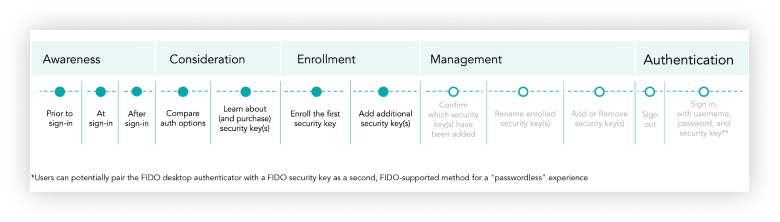
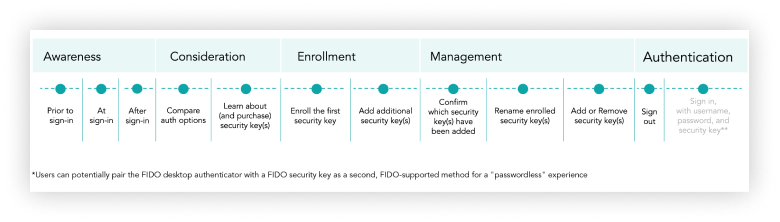
FIDO 安全密钥注册用户之旅:用户目标和流程步骤

端到端的用户体验以用户旅程的形式呈现。 FIDO安全密钥注册和身份验证用户流程包含多达12个流程步骤,是针对特定使用案例(即消费者在受监管行业网站上寻求使用FIDO安全密钥作为第二要素启用MFA)而开发的。 用户体验指南中提到的四个概念如下。
- 用户旅程:这可捕捉到用户在台式机/笔记本电脑端到端安全密钥注册和身份验证流程中的高层次目标和流程步骤。
- 流程步骤:每个旅程都分为 “登录时的认知 “和 “比较认证选项 “等流程步骤,这些步骤属于 “认知 “或 “考虑 “等高层次用户目标。
- 使用案例:这指的是《用户体验安全密钥指南》所针对的具体使用场景–消费者在受监管行业(如银行或医疗保健行业)基于浏览器的网站上将 FIDO 安全密钥作为第二要素启用 MFA。
- 使用安全密钥作为第二要素的 MFA 登录:这是指在 Windows 或 Mac OS 台式机/笔记本电脑上使用包含 FIDO 安全密钥作为第二要素的任何 MFA 登录。
FIDO 安全密钥注册用户旅程和测试站点

通过“注册网上银行 “链接设置用户名和密码。
_2.png)
使用用户名和密码登录数字银行。

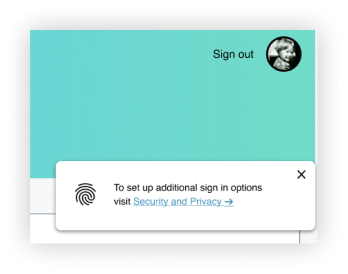
在“帐户交易”页面上,选择主导航栏或“个人资料”下的 “安全和隐私” 设置。 或者,点击祝酒词通知中的安全和隐私链接。
.png)
滚动到“安全和隐私设置”页面的底部,然后阅读 “了解详细信息” 以查看有关安全密钥的事实。
.png)
选择 “添加安全密钥”,输入密钥的昵称,然后选择 “继续”。
现在,您的 FIDO 密钥已注册为第二个身份验证因素!
如果您有另一个密钥,请现在添加,作为备份。 如果没有添加第二个密钥,请返回 “安全和隐私设置 “确认安全密钥注册信息,并找到从账户中重命名或删除密钥的选项。
注册 FIDO 安全密钥作为第二要素后,退出数字银行。 输入用户名和密码登录数字银行并连接密钥。
简单、快捷、安全!
让我们开始吧
现在,我们将针对安全密钥注册和身份验证过程中的每个用户目标,深入探讨 FIDO 部署建议和用户界面示例。
认识
目的:提高用户对仅密码身份验证的可用替代方法的认识,并引导用户访问安全和隐私设置,以管理新的登录选项,包括安全密钥。
这一步骤详细介绍了注册服务机构如何通过信息传递策略和网站信息架构更新相结合的方式,提高客户对仅密码身份验证的可用替代方案(即 FIDO 安全密钥和平台桌面身份验证器)的认识。 注册商可根据其目标客户群或业务范围,选择向客户推广平台验证器和/或安全密钥。 我们的用户研究表明,客户可能需要多次接触新的身份验证选项,才能采取行动设置新的登录方法。
建议
签到之前:
-
在网站之外,战略性地利用多种渠道宣传安全和隐私设置,将其作为优化账户安全的目的地。
- 在网站之外,利用电子邮件活动、家庭邮件和/或社交媒体,建议用户访问安全和隐私设置,了解并加强账户安全和设置 MFA,包括使用安全密钥。
- 在与客户就隐私和安全建议进行在线交流时,始终链接到安全和隐私设置页面。
- 考虑针对可能从使用安全密钥中获益最多的特定客户(如高净值银行客户),发送有关身份验证选项的教育材料,包括安全密钥的好处。
签到时
-
提高对只用密码的身份验证的替代方法的普遍认识,而不是专门宣传一种可能不熟悉的安全密钥方法:
- 对于在桌面网页上提供生物识别技术的注册用户,应在登录用户界面上显示用户熟悉的生物识别图标(即指纹),以表明用户可以使用生物识别登录或触摸解锁,从而替代仅凭密码的身份验证。
- 我们的研究表明,即使用户没有使用生物识别登录,指纹图标也会触发他们考虑使用非密码登录。
- 熟悉的指纹图标比具体提及未知的安全密钥概念更能引起用户对更新登录选项的兴趣。
- 不在桌面网页上提供生物识别技术的注册用户应考虑在登录用户界面上使用图标来表示更广泛的身份验证类别(例如,用户轮廓和复选标记或带有星号的锁来表示 PIN 码)。
- 在登录用户界面的验证图标旁,加入简短的静态信息作为行动号召,引导用户在登录后进入安全和隐私设置,设置新的登录选项。
- 对于在桌面网页上提供生物识别技术的注册用户,应在登录用户界面上显示用户熟悉的生物识别图标(即指纹),以表明用户可以使用生物识别登录或触摸解锁,从而替代仅凭密码的身份验证。
签到后
-
在网站内,通过更新网站架构和/或在网站上战略性地推广此设置链接,使安全和隐私设置成为管理账户安全的可发现目的地。
- 让安全和隐私设置在网站内更容易被发现。 在主网站导航中推广安全和隐私设置链接,或将其添加为 “个人资料 “下的唯一目的地(即在更通用的 “设置 “菜单项之外)。
-
在您的网站上,战略性地利用多种信息传递策略,将 “安全与隐私 “作为优化账户安全的目的地进行宣传。
- 为了激发多次实地考察的兴趣,请使用一种以上的信息传递形式。 例如,利用横幅广告或 “吐司 “通知等临时信息策略,邀请用户访问 “安全与隐私”,更新他们的登录方法。
- 要激发新登录方法的注册,尤其是安全密钥的采用,往往需要多次信息曝光。
- 注册安全密钥是一个多步骤的过程,需要投入时间和精力来了解、购买和注册安全密钥。
- 我们的研究表明,在其他网站目标的背景下,用户在采取行动之前往往需要多次接触设置新登录选项的想法。 让用户有多次机会注意到相关信息,并在方便时采取行动。
- 例如,在多次访问网站时显示祝酒辞通知,邀请用户访问安全和隐私设置以更新登录方法。
提高认识:推广安全和隐私设置以加强账户安全
用户界面示例
通过使安全和隐私设置成为更易发现的目的地,促进用户主动管理其账户安全和登录选项。
签到时
- 对于提供生物识别身份验证的网站,可在登录用户界面中使用生物识别图标(指纹)来告知用户可使用生物识别登录(即仅密码身份验证的替代方式)。
- 我们的研究表明,即使用户没有使用生物识别登录,指纹图标也会触发他们考虑只用密码登录的替代方案。
- 包含更新登录选项的持续行动号召(例如,”要设置新的登录选项,请在登录后访问安全和隐私”)。
签到后
- 采用祝酒辞通知,引导用户访问安全和隐私,添加新的登录选项。
- 在吐司通知上添加身份验证图标(例如,提供生物识别登录功能的注册表可添加指纹)。
- 在主账户导航中添加 “安全与隐私 “链接,或在用户配置文件菜单中添加 “设置 “链接。
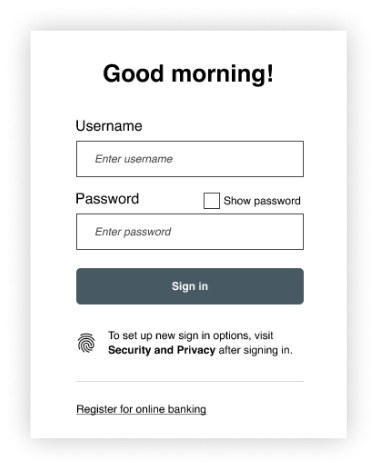
图 1 – 带指纹图标和行动呼吁文本的登录用户界面示例
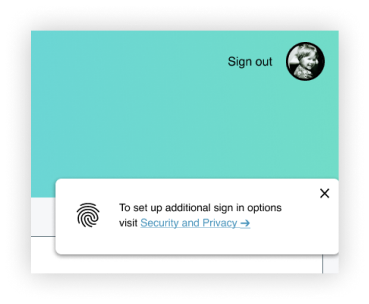
图 2 – 带有生物识别图标和安全与隐私设置链接的吐司通知
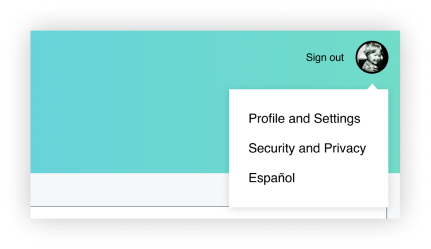
图 3 – 主导航或用户配置文件下的安全和隐私设置链接
考虑因素
目的:通过设计 “安全和隐私 “设置页面,帮助用户了解和比较可用的身份验证选项(包括安全密钥),让用户在保护自己的账户方面发挥积极作用。
越来越多的公司开始提供安全密钥,作为客户验证和保护账户的一种更有力的方式。 然而,我们的研究表明,大多数消费者并不熟悉将安全密钥作为消费者网站身份验证的一种选择。
向客户宣传安全密钥的优势、如何购买 FIDO 安全密钥以及如何通过注册多个密钥为账户恢复做好准备,可以帮助客户克服消费者采用安全密钥的障碍。
建议
通过提供符合以下标准的安全和隐私设置页面,帮助用户比较和了解网站上可用的身份验证选项,包括安全密钥:
-
明确建议用户在密码之外增加第二种身份验证方法,以提高账户的安全性。
- 确保用户可以删除此建议信息。
-
用图标讲故事。 故事便于用户记忆,而图标会讲故事。
- 在安全和隐私设置的建议信息中添加图标,以提高其可见度和视觉趣味性,并标明建议添加的方法,如平台验证器(如指纹图标)和安全密钥。
- 在身份验证方法名称旁边也使用图标,以区分每种方法并提高页面的可扫描性。
- 提供清晰的视觉指示器,标明用户当前使用的登录方式。
-
简要说明每种方法的认证流程和/或独特价值主张。
- 由于需要提高消费者对安全密钥的认识,我们建议强调安全密钥是第二要素(即在密码之外使用),可以使用多个安全密钥,并建议使用多个安全密钥。
- 文本示例:”安全密钥可让您在登录数字银行时更安全、更方便地完成两步验证。您可以添加任意数量的安全密钥”。
- 由于需要提高消费者对安全密钥的认识,我们建议强调安全密钥是第二要素(即在密码之外使用),可以使用多个安全密钥,并建议使用多个安全密钥。
-
在 “了解更多 “链接中逐步披露有关安全密钥和平台验证器的更多信息。
- 确保在安全密钥注册前后都能看到 “了解更多 “链接,因为当用户对使用安全密钥有疑问或担心时,这两个链接都是相关的接触点。
- 通过用户研究,我们确定了一些主题,以解决参与者对安全密钥的首要问题和顾虑,这些问题和顾虑是采用安全密钥的潜在障碍。
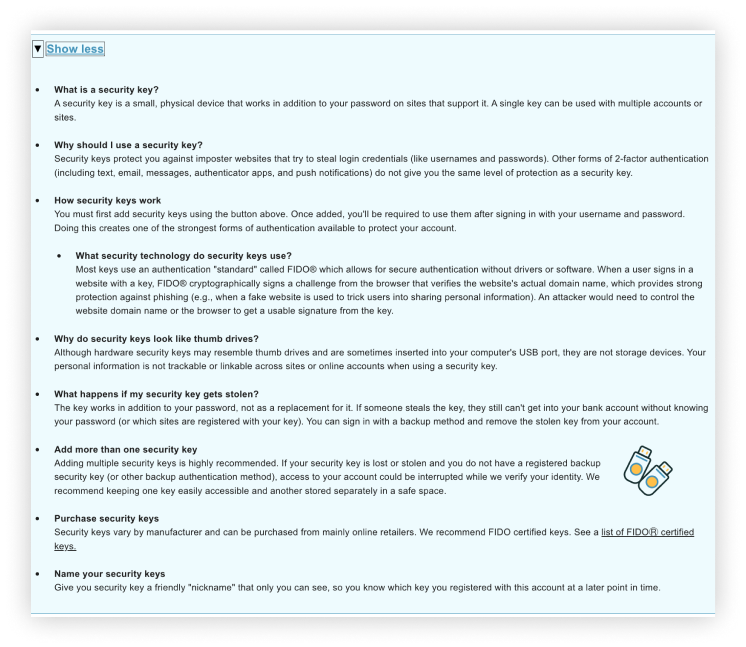
图 4 – 基于证据的 “了解更多 “内容,内容涉及
通过多轮用户研究开发的安全密钥
考虑:安全和隐私设置页面
用户界面示例
在祝酒词通知、主网站导航和/或用户配置文件中,将用户链接到安全和隐私设置页面,其中包括以下内容:
- 建议信息:增加一种额外的登录方法,带有生物识别和安全密钥图标,用户可自行解 除。
- 注册状态指示器或标签,帮助用户快速识别当前正在使用的方法和仍可使用的方法
- 安全密钥部分有一个图标,并简要说明安全密钥的价值及其作为第二个身份验证因素的作用;包括建议使用多个密钥
- 在注册安全密钥前后都能看到 “了解更多 “链接
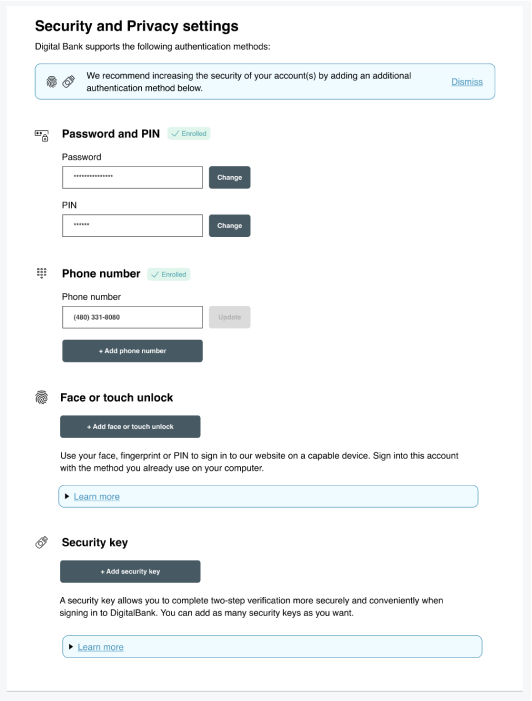
图 5 – 安全和隐私设置页面(注册安全密钥前)
入学率
目的:允许用户使用 FIDO 安全密钥作为第二要素进行身份验证,并注册其他密钥(立即注册或稍后注册),以便恢复账户。
建议
- 鼓励使用多个密钥:在多个接触点,大力鼓励用户添加一个以上的密钥,用于账户恢复和备份。
- 支持更新、添加和删除密钥: 对于每一种身份验证方法,包括安全密钥,都要提供明确的功能,以便更新现有的身份验证信息(如 “更改 “或 “更新 “按钮),删除当前使用的身份验证方法(如 “删除 “按钮),或在用户配置文件中添加新的身份验证方法(如 “添加 “按钮)。
- 重申使用安全密钥的价值主张:例如,”安全密钥可让您在登录数字银行时更方便、更安全地完成两步验证”。
- 增加用户添加昵称的功能:开始注册时,要求用户输入自己选择的昵称,以便日后识别注册的密钥。
- 指定昵称只对用户可见(即不等同于需要保密的密码),并在将来提醒用户注册了哪些密钥。
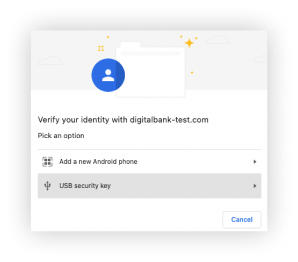
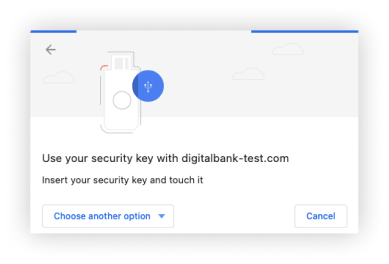
- 调用 FIDO API,让浏览器和/或操作系统处理剩余的安全密钥注册用户界面。
- 可选的验证步骤: 作为安全密钥注册流程的一部分,贵机构可配置网站要求验证(即要求用户允许与网站共享制造商信息,如安全密钥的品牌和型号)。 如果可以从安全密钥制造商处获得详细信息,那么在用户的账户注册安全密钥后,就可以通过认证向用户显示品牌和型号。
- FIDO Alliance不建议在消费者用户案例中添加这一证明步骤,因为它要求用户在安全密钥注册过程中通过额外的对话授予网站权限。
- 如果贵组织选择更简单的注册流程,则可以关闭验证,绕过权限对话。 采用这种方案后,客户日后将无法获得钥匙品牌和型号的详细信息。
- 增加这一额外的证明步骤可能对劳动力方案的安全密钥注册很有价值。
- 可选的用户验证步骤: 作为安全密钥注册过程的一部分,贵组织也可以选择配置网站,要求用户验证,即要求用户添加 PIN 或指纹,以验证安全密钥。 这个可选的验证步骤不在本用户体验指南的研究范围之内。
-
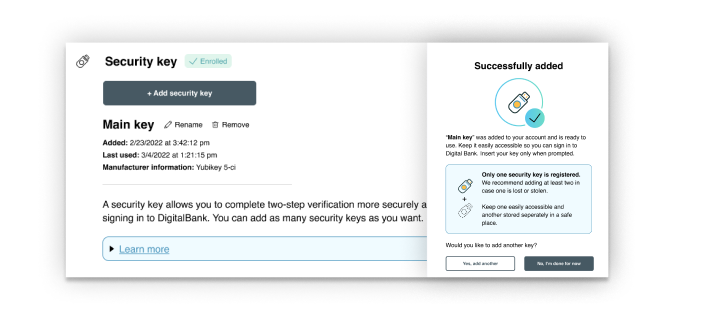
在安全密钥注册登陆页面上显示注册成功或出错信息。
- 如果安全密钥注册成功,则显示成功信息,并带有安全密钥图标和成功的可视化指示符(如安全密钥图标旁的复选标记)。
- 如果安全密钥注册失败,请显示错误信息,帮助用户了解注册失败,并允许他们重新启动注册过程。
-
在多个接触点,鼓励用户添加第二个安全密钥,用于账户恢复和备份。
- 在注册安全密钥之前,在安全和隐私设置页面上提供信息,鼓励用户添加多个密钥。
- 在注册安全密钥后,应立即强烈建议并提供添加第二个安全密钥的机会,要求用户暂停并考虑这一建议。
-
在 “密钥已成功添加 “屏幕上,使用多种策略强调应使用两个或更多安全密钥:
- 标题:创建一个标题,用粗体字强调 “只注册一个安全密钥”。
- 文本:明确建议至少增加两把安全钥匙,以防一把安全钥匙丢失或被盗。
- 插图:使用插图强调只注册一个安全密钥的状态和注册两个安全密钥的理想状态。
- “添加第二个密钥 “选项:提供两个操作按钮(”完成 “和 “添加第二个密钥”),它们同样可见和易用,默认操作为 “完成”,因为大多数参与者可能还没准备好立即添加另一个安全密钥。
注册:使用 FIDO 安全密钥作为第二因素进行身份验证,并添加其他密钥
用户界面示例
“添加安全密钥 “注册页面应包括以下内容:
- 退出注册过程的能力
- 安全密钥图标或图像
- 将安全密钥作为第二要素身份验证方法的信息传递
- 要求添加安全密钥昵称
- 指定安全密钥只对用户可见(即不等同于需要保密的密码)
- 指定昵称用于提醒用户以后注册了哪些安全密钥的信息
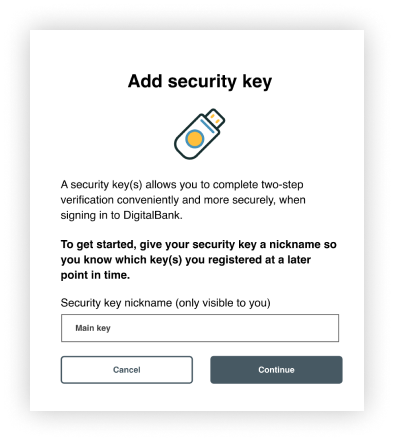
图 6 – 添加安全密钥页面
“成功添加 “屏幕应包括以下内容:
- 安全密钥图标,直观显示注册成功(如复选标记)
- 用户定义的安全密钥昵称
- 提醒您保持安全密钥便于登录使用
- 提醒用户只能注册一把密钥,并建议用户添加多把安全密钥,以防丢失或被盗
- 指示将一把安全钥匙放在容易拿到的地方,另一把存放在安全的地方
- 主要操作按钮应该是对问题 “您想添加另一个安全密钥吗?”的二进制回答。 包含两个同样突出的操作按钮,包括选项(是,再添加一个)。
- 默认情况下使用 “完成 “操作按钮,因为大多数用户不可能随身携带另一个安全密钥来进行注册
- 表示未成功注册的图标和文字
- 明确的操作按钮,用于重新启动安全密钥注册或取消注册
98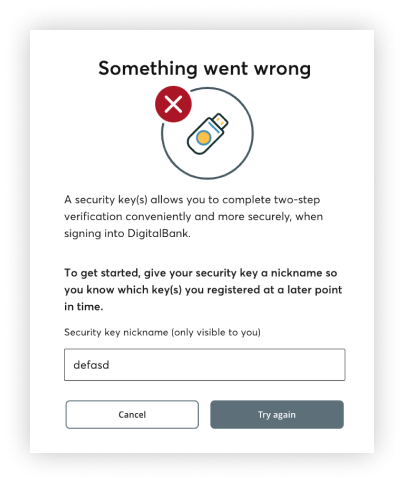
图 8 – Mac 用户的 FIDO 注册后登录
管理层
目的:帮助用户确认已注册的安全密钥、注册安全密钥的时间以及上次使用的时间。 提供清晰、可发现的选项,用于重命名和删除已注册的安全密钥,以及添加其他安全密钥。
建议
-
注册后,返回安全和隐私设置(除非用户要添加新的安全密钥)。 在页面上显示相关的安全关键数据,无需用户深入查看。
- 包括以下安全密钥信息:
- 关键昵称
- 添加日期
- 最后使用日期
- 安全密钥制造商信息(如果验证已打开,且用户选择共享)
- 包括以下安全密钥信息:
- 在 “安全和隐私 “设置的 “安全密钥 “部分显示 “添加密钥 “按钮,作为主要操作呼吁
- 为用户提供一个可见选项,用新的昵称重新命名安全密钥。
-
为用户提供从账户中删除安全密钥的可见选项。
- 确认用户是否要删除
。 - 显示一个图标,直观地表示 “移除”,例如在安全密钥上方显示一个红色减号。
- 确认用户是否要删除
用户界面示例
注册后,除非用户选择添加第二个安全密钥,否则应立即返回 “安全和隐私 “设置。
在 “安全和设置 “页面,显示安全密钥数据,帮助用户确认注册是否成功,以及是否发生了未经授权使用安全密钥的情况。 授权用户更新安全密钥昵称或取消安全密钥注册,包括
- 关键昵称
- 添加和最后使用日期
- 认证安全密钥制造商信息(可选)
- 持续将 “添加密钥 “选项作为主要行动呼吁
- “重命名 “和 “删除 “选项
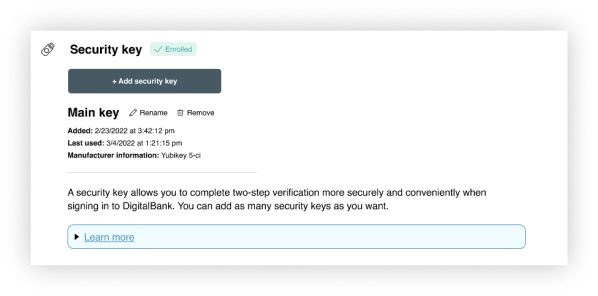
图 9 – 安全和隐私设置页面(注册安全密钥后)
认证
目的:允许已注册 FIDO 安全密钥的用户在输入用户名和密码后使用其安全密钥作为第二要素登录。
建议
-
注册安全密钥后,不要更改第一要素(即用户名和密码)登录体验
- 用户研究表明,更新主页以告知账户已添加安全密钥被视为侵犯隐私和安全。
-
保留二级非 FIDO 安全密钥登录路径
- 提供 “切换用户 “和 “以其他方式登录 “链接,以保留多用户访问权限和用户在账户中注册的其他辅助身份验证方法。
-
输入用户名和密码后,提示用户连接安全密钥。
- 提供一个选项(如 “使用安全密钥 “按钮),让用户主动连接安全密钥,而不是自动启动浏览器对话连接安全密钥。
- 用户主动连接安全密钥确实会带来额外的点击次数,但这有助于确保在用户手头没有安全密钥时,浏览器对话不会超时。
- 我们的研究表明,直接进入操作系统/浏览器对话框会让那些没有安全密钥的用户感到焦虑。 当找回安全密钥导致浏览器对话超时并要求用户重新启动注册过程时,用户也会感到沮丧。
-
签出
- 一旦用户注册了 FIDO 安全密钥,请确保他们只需输入用户名和密码,就能使用与以前相同的用户界面退出网站。
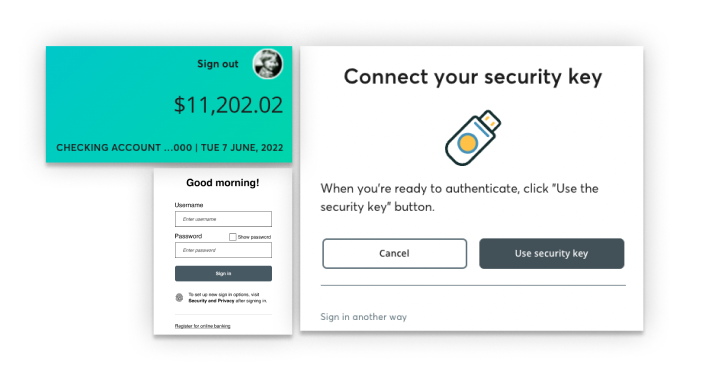
用户界面示例
- 注册安全密钥后,输入用户名和密码的登录用户界面应与注册前一致。
- 登录时,用户输入用户名和密码后,显示带有安全密钥图标的 “连接安全密钥 “页面。
- 允许用户通过 “使用安全密钥 “按钮启动密钥连接。
- 包括取消选项。
- 加入 “以其他方式登录 “选项,确保用户在无法使用密钥时可以使用备用方法。
- 注册安全密钥后,签出用户界面应与注册前一致。
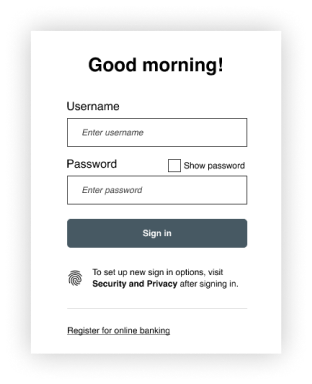
图 10 – 注册安全密钥后的登录用户界面
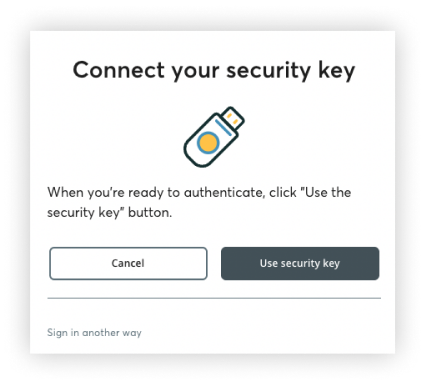
图 11 -连接安全密钥提示,作为登录时的第二个身份验证因素
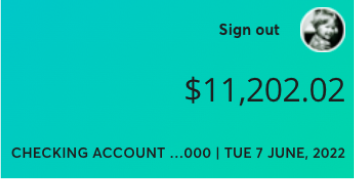
图 12 -注册安全密钥后的退出用户界面
利用 FIDO 安全密钥优化客户成功体验
目的:了解提高用户成功率和采用率的有用策略。
-
使用熟悉的认证语言和符号进行引导
- 与其明确推广陌生的安全密钥概念,不如推广使用熟悉的指纹图标(如果支持生物识别技术)或其他代表身份验证的图像(如 PIN 的锁和星号)来替代仅凭密码的登录方式。
-
推广 “安全和隐私 “设置页面,将其作为管理和学习账户安全(特别是安全密钥)的现场中心
- 鼓励用户访问 “安全和隐私 “设置页面,以方便发现作为登录选项的安全密钥。 创造一种环境,让用户了解安全密钥的性质和优势,并采取行动识别安全密钥,购买和/或注册安全密钥。
-
让用户了解安全密钥的工作原理,从而树立信心和信任。
- 越来越多的网站开始提供用于身份验证的安全密钥,但我们的研究表明,缺乏用户教育是采用安全密钥的一个障碍。
- 我们的研究表明,安全密钥与 USB 驱动器的相似性导致一些潜在用户担心安全密钥可能含有恶意软件或病毒,当用户将安全密钥插入机器时,病毒可能会自动感染机器。 在 “了解更多 “文本中说明安全密钥的工作原理并将其与 USB 驱动器区分开来,可以让用户放心,并消除采用安全密钥的障碍。
-
为客户支持做好准备,了解以下知识
- 如何使用 FIDO 安全密钥注册和进行身份验证
- 哪些安全密钥已通过 FIDO 认证并与您的网站兼容
- 为什么说 FIDO 安全密钥是安全、可靠、方便的网站身份验证替代方案?
- 大力鼓励用户注册多个安全密钥,以帮助确保用户在安全密钥丢失或被盗时不会被阻止访问其账户。
-
宣传您的品牌与FIDO Alliance之间的合作关系。
- 客户对相对陌生的 FIDO 品牌元素的信任,首先来自于 FIDO 与您值得信赖的品牌之间的关联。
- 此外,具有安全意识的消费者更有可能了解 FIDO 标准,也更有可能使用他们的安全密钥。
FIDO 安全密钥用户体验指南术语表
持续发送信息:
在用户界面中以一致的位置持续显示的信息文本。 持久信息发送有助于确保如果用户在某次访问中错过了某条信息,该信息仍会留在原来的位置,供用户以后理解或采取行动(如果需要的话)。
临时消息:
在屏幕上显示一定时间后消失的简短信息,可用于吸引用户注意。 例如,”祝酒词 “通知的新颖性和动感比持续性信息更能吸引用户的注意力。 这类通知不应掩盖用户数据,用户应可自行解除,也不应用于阻碍用户继续执行任务流程的错误。
逐步公开:
一种交互设计技术,将信息和选项在一个以上的屏幕上进行排序,以减少用户的不知所措感。 循序渐进的信息披露让重要信息触手可及,而不会让用户在同一时间接触到所有相关信息、操作或任务。
安全钥匙
我们建议在整个用户界面中使用 “安全密钥 “术语(而不是 USB 密钥或钥匙)。
专业消费者:
在本文件中,”专业消费者 “是指在个人生活中较早采用安全和隐私技术和服务的具有安全和隐私意识的消费者。

.png)
