作者:Salah Machani,RSA,Dell Technologies 业务部;FIDO 企业采用小组联合主席
FIDO 联盟开发了一个易于使用和部署的强多因素身份验证 (MFA) 框架。 许多企业已经部署了联合身份验证,以跨本地或云应用程序启用单点登录 (SSO)。 当企业考虑部署和利用 FIDO 进行更强大的身份验证时,他们会质疑 FIDO 是否旨在取代现有的联合协议,或者是否需要进行全面改革才能将 FIDO 与这些现有协议集成。 答案是否定的:FIDO 和联合协议不仅是互补的,而且可以最佳地协同工作。
FIDO 联盟发布了一份白皮书,详细介绍了 FIDO 如何补充联合协议,并提供了有关如何集成两者的指南,以增加对基于 FIDO 的 MFA 的支持,并替换或补充联合环境中的传统身份验证方法。
FIDO 的主要目标是减轻记住多个密码或为单独的应用程序使用各种双因素身份验证外形规格的负担。 当用户向应用程序提供商注册启用了 FIDO 的设备(例如安全密钥或移动设备)时,将生成一个唯一的凭据,并将其绑定到该特定应用程序提供商的用户帐户。 用户可以使用相同的启用了 FIDO 的设备,并重复该过程,为其他应用程序提供程序的用户生成其他唯一凭据,而无需携带其他设备。 用户设备上的凭据通常使用相同的本地 PIN 或生物识别技术进行锁定,允许用户使用单个简单的手势跨多个应用程序进行身份验证。
安全断言标记语言 (SAML) 和 OpenID Connect (OIDC) 等联合协议旨在将用户身份转移到受信任的第三方身份验证机构,并远离应用程序和服务提供商。 当用户向受信任的身份验证颁发机构进行身份验证时(通常使用密码),将发出有时限的断言或令牌,供该用户提供给一个或多个应用程序提供程序。 用户不需要向身份验证机构或每个应用程序提供程序重新进行身份验证,这是 SSO 的定义。
企业在向应用程序发起“登录”请求或“升级”用户会话的身份验证时,使用 FIDO 身份验证器对用户进行身份验证。 在联合环境中,可以部署 FIDO 以支持以下两种方案
在初始登录方案中,应用程序提供程序将用户重定向到应用程序颁发机构(在本
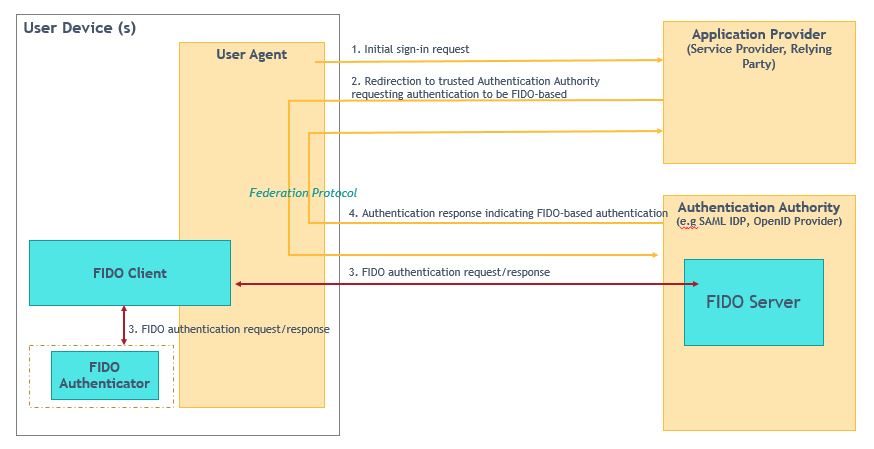
图 1:使用基于 FIDO 的身份验证进行初始“登录”
在升级方案中,在身份验证机构使用特定身份验证机制执行初始用户身份验证并被重定向到应用程序提供程序并断言该事实之后。 随后,应用程序提供程序确定该断言对特定资源请求的置信度不足。 因此,应用程序提供程序使用基于 FIDO 的机制执行其他身份验证,或者将用户重定向回身份验证机构,请求使用基于 FIDO 的身份验证重新对用户进行身份验证,以补充先前的非基于 FIDO 的身份验证,或者需要更高确定性的基于 FIDO 的身份验证来补充以前较低确定的基于 FIDO 的身份验证。 图 2 说明了在联合环境中使用 FIDO 进行递进式身份验证的通用工作流程。
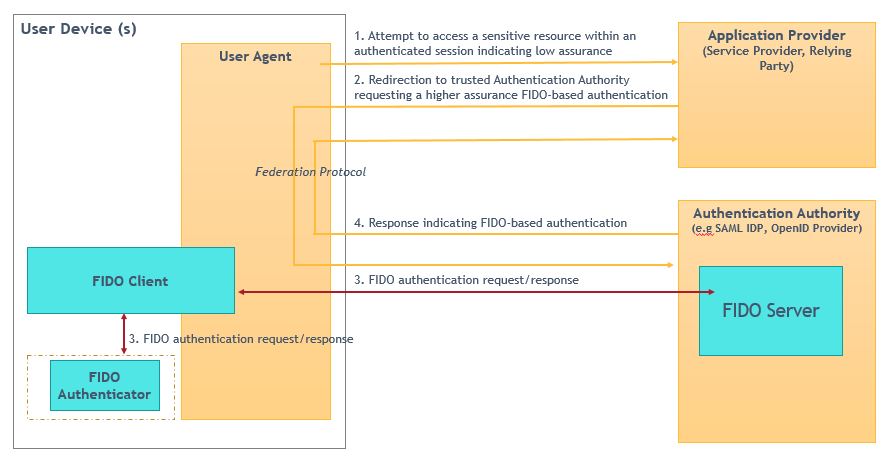
图 2:使用基于 FIDO 的身份验证进行“升级”
这两种方案集成的全部价值假定现有应用程序可以请求身份验证机构进行基于 FIDO 的身份验证,或使用特定的 FIDO 身份验证器。 对基于 FIDO 的身份验证的请求可以是显式的,也可以是隐式的,方法是指示需要 FIDO 身份验证器的策略名称或保证级别。 或者,默认情况下,身份验证机构可以对所有用户、一组用户或在应用程序提供商预定义的某些条件下强制执行基于 FIDO 的身份验证。
通过允许用户向受信任的身份验证机构注册 FIDO 身份验证器,然后跨应用程序使用该 FIDO 身份验证器,而无需直接向每个应用程序注册,联合身份验证可增强用户体验、提高安全性并“放大”FIDO 部署。
需要注意的是,FIDO 和联合协议中的信任模型是不同的。
- 使用 FIDO,用户和应用程序提供程序之间存在直接信任。 应用程序提供程序在其基础结构中部署 FIDO 服务器,以存储用户的公共凭据并直接对用户进行身份验证。 应用程序提供程序称为 FIDO 信赖方 (RP)。
- 使用联合协议时,用户和应用程序提供者之间的信任是间接的。 在用户和认证机构之间以及认证机构和应用程序提供商之间建立信任。 用户向认证机构进行认证,认证机构向应用程序提供程序发出有关用户身份的断言。
在组合的 FIDO 和联合环境中,身份验证颁发机构充当 FIDO RP。
FIDO 满足了快速变化的企业环境的新兴需求,而且还扩展和构建了传统协议(如联合协议),以保留现有功能和工作流。 这样,企业就可以以最具成本效益的方式利用 FIDO 的安全性和可用性优势。 要了解更多信息,请下载并阅读白皮书。
在本文中,您将找到有关如何将 FIDO 与领先的联合协议(即 SAML、OIDC 和 OAuth)集成的详细信息,包括:
- SAML 服务提供商 (SP) 从 SAML 身份提供商 (IDP) 请求用户身份验证基于 FIDO。
- SAML IDP 向 SP 返回一个 SAML 断言,指示用户身份验证是使用 FIDO 执行的。
- 来自 OIDC 提供程序的 OIDC RP 请求身份验证基于 FIDO。
- OIDC 提供程序向 RP 返回一个令牌,指示用户身份验证是使用 FIDO 执行的,以及如何执行。
- 在用户同意和授权访问受保护资源之前,可以在 OAuth2 环境中利用 FIDO 进行用户身份验证。
FIDO 技术说明重点介绍了 FIDO 规范中对从业者来说很重要的方面。 技术说明阐明了架构选择,解释了最佳实践,并为技术部署者提供了指导。 技术说明是正在进行的 FIDO 系列的一部分,该系列以 FIDO 联盟的技术和演变为特色。

