Abstract
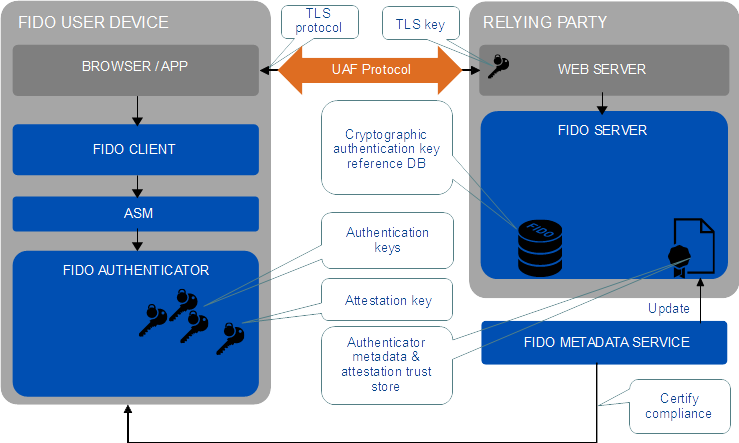
The FIDO UAF strong authentication framework enables online
services and websites, whether on the open Internet or within
enterprises, to transparently leverage native security features
of end-user computing devices for strong user authentication and
to reduce the problems associated with creating and remembering
many online credentials. The FIDO UAF Reference Architecture
describes the components, protocols, and interfaces that make
up the FIDO UAF strong authentication ecosystem.
Status of This Document
This section describes the status of this document at the time of its publication.
Other documents may supersede this document. A list of current FIDO Alliance publications and the
latest revision of this technical report can be found in the FIDO Alliance specifications index at
https://www.fidoalliance.org/specifications/.
This document was published by the FIDO Alliance as a Review Draft.
This document is intended to become a FIDO Alliance Proposed Standard.
If you wish to make comments regarding this document, please
Contact Us.
All comments are welcome.
This is a Review Draft Specification and
is not intended to be a basis for any implementations as the Specification may change. Permission is
hereby granted to use the Specification solely for the purpose of reviewing the Specification. No rights
are granted to prepare derivative works of this Specification. Entities seeking permission to reproduce
portions of this Specification for other uses must contact the FIDO Alliance to determine whether an
appropriate license for such use is available.
Implementation of certain elements of this Specification may require licenses under third party intellectual
property rights, including without limitation, patent rights. The FIDO Alliance, Inc. and its Members
and any other contributors to the Specification are not, and shall not be held, responsible in any manner
for identifying or failing to identify any or all such third party intellectual property rights.
THIS FIDO ALLIANCE SPECIFICATION IS PROVIDED “AS IS” AND WITHOUT ANY
WARRANTY OF ANY KIND, INCLUDING, WITHOUT LIMITATION, ANY EXPRESS OR IMPLIED
WARRANTY OF NON-INFRINGEMENT, MERCHANTABILITY OR FITNESS FOR A
PARTICULAR PURPOSE.
1. Introduction
This section is non-normative.
This document describes the FIDO Universal Authentication
Framework (UAF) Reference Architecture. The target audience for
this document is decision makers and technical architects who
need a high-level understanding of the FIDO UAF strong
authentication solution and its relationship to other relevant
industry standards.
The FIDO UAF specifications are as follows:
- FIDO UAF Protocol
- FIDO UAF Application API and Transport Binding
- FIDO UAF Authenticator Commands
- FIDO UAF Authenticator-Specific Module API
- FIDO UAF Registry of Predefined Values
- FIDO UAF APDU
The following additional FIDO documents provide important information relevant to the UAF specifications:
- FIDO AppID and Facets Specification
- FIDO Metadata Statements
- FIDO Metadata Service
- FIDO Registry of Predefined Values
- FIDO ECDAA Algorithm
- FIDO Security Reference
- FIDO Glossary
These documents may all be found on the FIDO Alliance website at
http://fidoalliance.org/specifications/download/
1.1 Background
This section is non-normative.
The FIDO Alliance mission is to change the nature of online
strong authentication by:
- Developing technical specifications defining open, scalable,
interoperable mechanisms that supplant reliance on passwords to
securely authenticate users of online services.
- Operating industry programs to help ensure successful worldwide
adoption of the specifications.
- Submitting mature technical specifications to recognized
standards development organization(s) for formal
standardization.
The core ideas driving the FIDO Alliance's efforts are 1) ease
of use, 2) privacy and security, and 3) standardization. The
primary objective is to enable online services and websites,
whether on the open Internet or within enterprises, to leverage
native security features of end-user computing devices for
strong user authentication and to reduce the problems
associated with creating and remembering many online
credentials.
There are two key protocols included in the FIDO architecture
that cater to two basic options for user experience when
dealing with Internet services. The two protocols share many of
underpinnings but are tuned to the specific intended use cases.
Universal Authentication Framework (UAF) Protocol
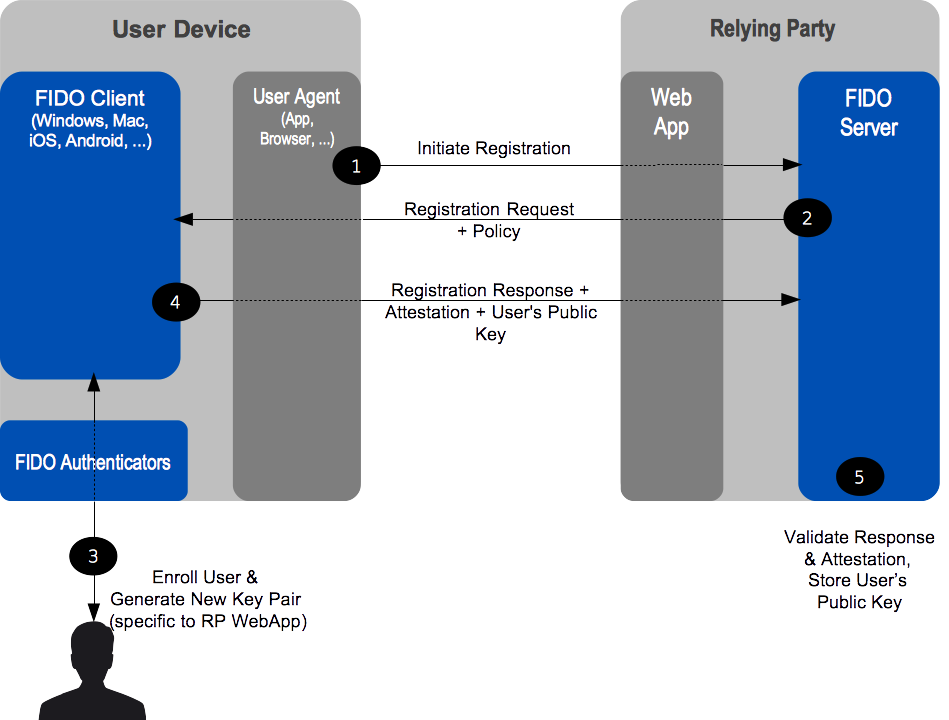
The UAF protocol allows online services to offer password-less
and multi-factor security. The user registers their device to
the online service by selecting a local authentication
mechanism such as swiping a finger, looking at the camera,
speaking into the mic, entering a PIN, etc. The UAF protocol
allows the service to select which mechanisms are presented to
the user.
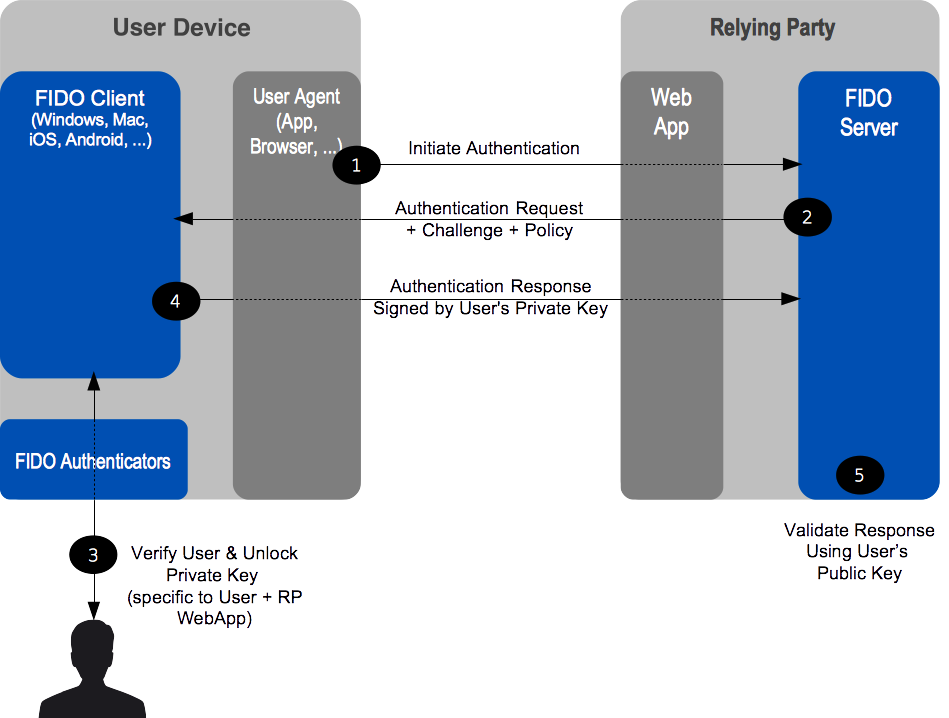
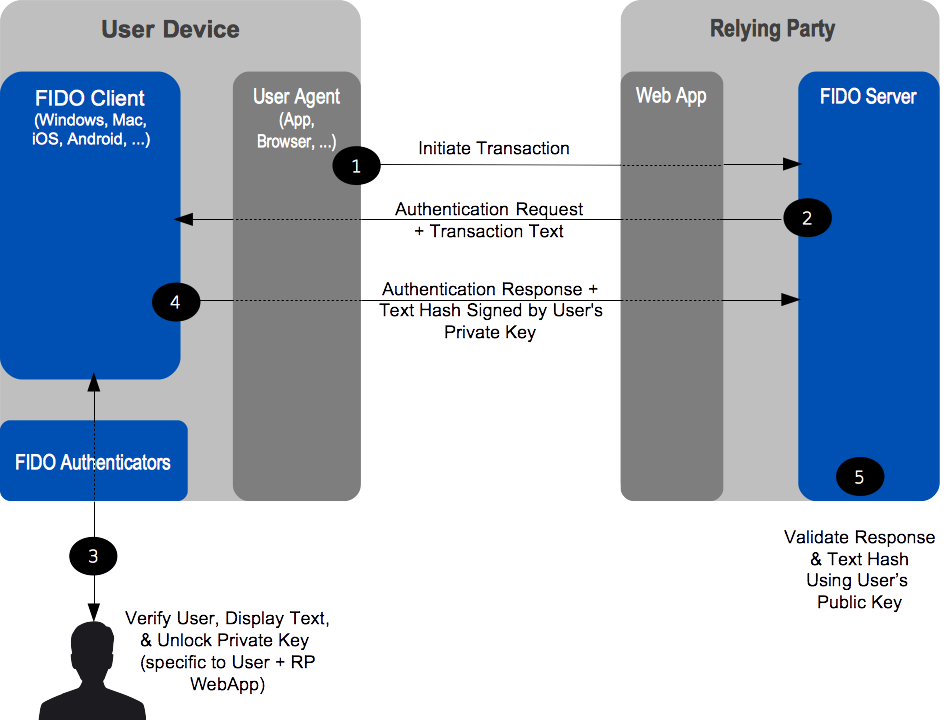
Once registered, the user simply repeats the local
authentication action whenever they need to authenticate to the
service. The user no longer needs to enter their password when
authenticating from that device. UAF also allows experiences
that combine multiple authentication mechanisms such as
fingerprint + PIN.
This document that you are reading describes the UAF reference
architecture.
Universal 2nd Factor (U2F) Protocol
The U2F protocol allows online services to augment the security
of their existing password infrastructure by adding a strong
second factor to user login. The user logs in with a username
and password as before. The service can also prompt the user to
present a second factor device at any time it chooses. The
strong second factor allows the service to simplify its
passwords (e.g. 4-digit PIN) without compromising security.
During registration and authentication, the user presents the
second factor by simply pressing a button on a USB device or
tapping over NFC. The user can use their FIDO U2F device across
all online services that support the protocol leveraging
built-in support in web browsers.
Please refer to the FIDO website for an overview and
documentation set focused on the U2F protocol.
6. OATH, TCG, PKCS#11, and ISO 24727
These are either initiatives (OATH, Trusted Computing Group
(TCG)), or industry standards (PKCS#11, ISO 24727). They all
share an underlying focus on hardware authenticators.
PKCS#11 and ISO 24727 define smart-card-based authenticator
abstractions.
TCG produces specifications for the Trusted Platform Module, as
well as networked trusted computing.
OATH, the "Initiative for Open AuTHentication", focuses on
defining symmetric key provisioning protocols and
authentication algorithms for hardware One-Time Password (OTP)
authenticators.
The FIDO framework shares several core notions with the
foregoing efforts, such as an authentication abstraction
interface, authenticator attestation, key provisioning, and
authentication algorithms. FIDO's work will leverage and extend
some of these specifications.
Specifically, FIDO will complement them by addressing:
- Authenticator discovery
- User experience
- Harmonization of various authenticator types, such as biometric,
OTP, simple presence, smart card, TPM, etc.
1. Also known as: Authentication Tokens, Security Tokens, etc.↩
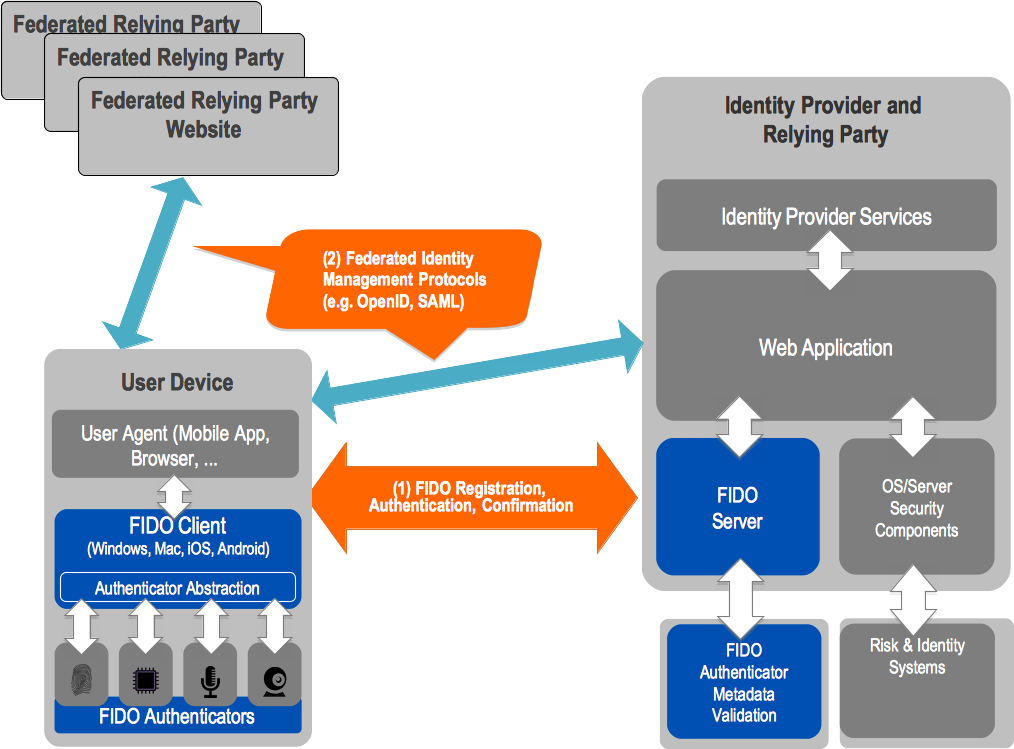
2. FIM protocols typically convey IdP <-> RP interactions through
the browser via HTTP redirects and POSTs.↩