Abstract
The FIDO Authenticator Metadata Specification defines
so-called "Authenticator Metadata" statements. The metadata statements contain
the "Trust Anchor" required to validate the attestation object, and
they also describe several other important characteristics of the
authenticator.
The metadata service described in this document
defines a baseline method for relying parties to access the latest
metadata statements.
Status of This Document
This section describes the status of this document at the time of its publication.
Other documents may supersede this document. A list of current FIDO Alliance publications and the
latest revision of this technical report can be found in the FIDO Alliance specifications index at
https://www.fidoalliance.org/specifications/.
This document was published by the FIDO Alliance as a Review Draft.
This document is intended to become a FIDO Alliance Proposed Standard.
If you wish to make comments regarding this document, please
Contact Us.
All comments are welcome.
This is a Review Draft Specification and
is not intended to be a basis for any implementations as the Specification may change. Permission is
hereby granted to use the Specification solely for the purpose of reviewing the Specification. No rights
are granted to prepare derivative works of this Specification. Entities seeking permission to reproduce
portions of this Specification for other uses must contact the FIDO Alliance to determine whether an
appropriate license for such use is available.
Implementation of certain elements of this Specification may require licenses under third party intellectual
property rights, including without limitation, patent rights. The FIDO Alliance, Inc. and its Members
and any other contributors to the Specification are not, and shall not be held, responsible in any manner
for identifying or failing to identify any or all such third party intellectual property rights.
THIS FIDO ALLIANCE SPECIFICATION IS PROVIDED “AS IS” AND WITHOUT ANY
WARRANTY OF ANY KIND, INCLUDING, WITHOUT LIMITATION, ANY EXPRESS OR IMPLIED
WARRANTY OF NON-INFRINGEMENT, MERCHANTABILITY OR FITNESS FOR A
PARTICULAR PURPOSE.
1. Notation
Type names, attribute names and element names are written as code.
String literals are enclosed in “”, e.g. “UAF-TLV”.
In formulas we use “|” to denote byte wise concatenation
operations.
The notation base64url(byte[8..64]) reads as 8-64 bytes of data
encoded in base64url, "Base 64 Encoding with URL and Filename
Safe Alphabet" [RFC4648] without padding.
Following [WebIDL-ED], dictionary members are optional unless they are
explicitly marked as required.
WebIDL dictionary members MUST NOT have a value of null.
Unless otherwise specified, if a WebIDL dictionary member is DOMString,
it MUST NOT be empty.
Unless otherwise specified, if a WebIDL dictionary member is a List,
it MUST NOT be an empty list.
UAF specific terminology used in this document is defined in
[FIDOGlossary].
All diagrams, examples, notes in this specification are non-normative.
Note
Note: Certain dictionary members need to be present in order to
comply with FIDO requirements. Such members are marked in the
WebIDL definitions found in this document, as
required. The keyword required has been
introduced by [WebIDL-ED], which is a work-in-progress. If you
are using a WebIDL parser which implements [WebIDL], then you
may remove the keyword required from your WebIDL and
use other means to ensure those fields are present.
1.1 Key Words
The key words “MUST”, “MUST NOT”, “REQUIRED”, “SHALL”, “SHALL
NOT”, “SHOULD”, “SHOULD NOT”, “RECOMMENDED”, “MAY”, and
“OPTIONAL” in this document are to be interpreted as
described in [RFC2119].
4. Considerations
This section is non-normative.
This section describes the key considerations for designing this metadata service.
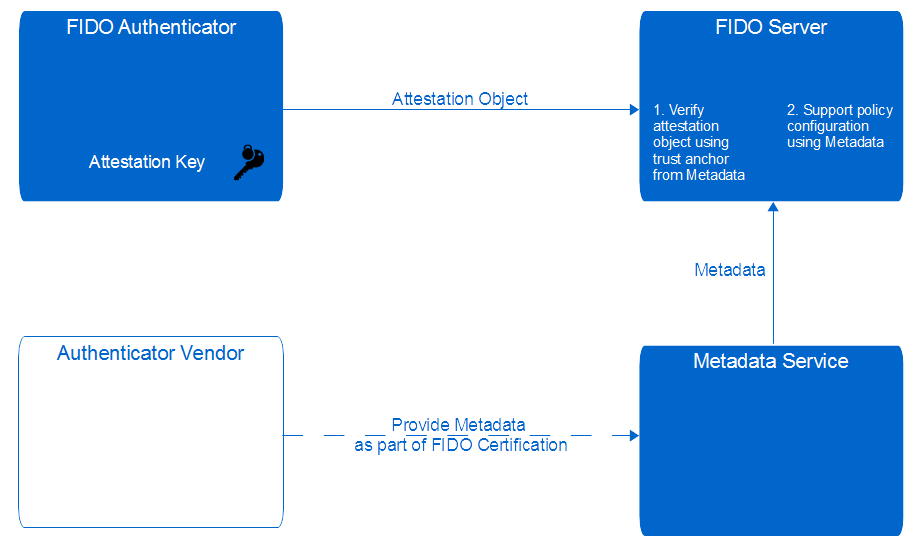
Need for Authenticator Metadata When defining policies for
acceptable authenticators, it is often better to describe the
required authenticator characteristics in a generic way than to
list individual authenticator AAIDs. The metadata statements
provide such information. Authenticator metadata also provides
the trust anchor required to verify attestation objects.
The metadata service provides a standardized method to access such metadata statements.
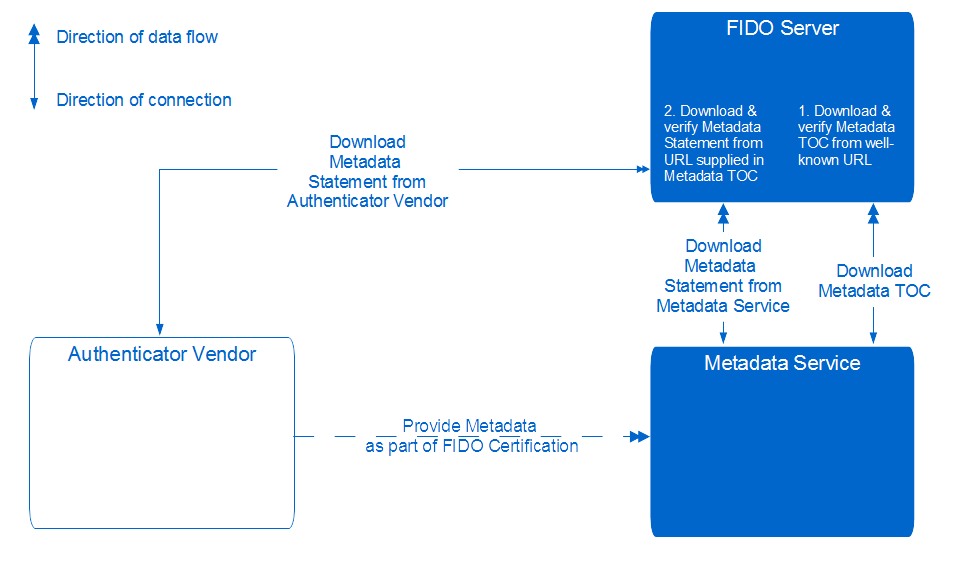
Integrity and Authenticity Metadata statements include
information relevant for the security. Some business verticals might even
have the need to document authenticator policies and trust anchors
used for verifying attestation objects for auditing purposes.
It is important to have a strong method to verify and proof
integrity and authenticity and the freshness of metadata
statements. We are using a single digital signature to protect
the integrity and authenticity of the Metadata TOC object and we
protect the integrity and authenticity of the individual metadata
statements by including their cryptographic hash values into the
Metadata TOC object. This allows for flexible distribution of the
metadata statements and the Metadata TOC object using standard
content distribution networks.
Organizational Impact Authenticator vendors can delegate
the publication of metadata statements to the metadata service in
its entirety. Even if authenticator vendors choose to publish
metadata statements themselves, the effort is very limited as the
metadata statement can be published like a normal document on a
website. The FIDO Alliance has control over the FIDO
certification process and receives the metadata as part of that
process anyway. With this metadata service, the list of known
authenticators needs to be updated, signed and published
regularly. A single signature needs to be generated in order to
protect the integrity and authenticity of the metadata TOC object.
Performance Impact Metadata TOC objects and metadata statements can be cached by the
FIDO Server.
The update policy can be specified by the
relying party.
The metadata TOC object includes a date for the next scheduled update.
As a result there is no additional impact to the FIDO Server
during FIDO Authentication or FIDO Registration operations.
Updating the Metadata TOC object
and metadata statements can be performed asynchronously.
This reduces the availability requirements for the metadata service and the load for the FIDO Server.
The metadata TOC object itself is relatively small as it does not contain the individual metadata statements.
So downloading the metadata TOC object does
not generate excessive data traffic.
Individual metadata statements are expected to change
less frequently than the metadata TOC object. Only the
modified metadata statements need be downloaded by the FIDO Server.
Non-public Metadata Statements Some authenticator vendors might want to provide access to
metadata statements only to their subscribed customers.
They can publish the metadata statements on access protected URLs. The access URL and
the cryptographic hash of the metadata statement is included
in the metadata TOC object.
High Security Environments Some high security environments might only trust
internal policy authorities. FIDO Servers in such environments
could be restricted to use metadata TOC objects from a proprietary trusted source only.
The metadata service is the baseline for most relying parties.
Extended Authenticator Information Some relying parties might want additional information
about authenticators before accepting them. The
policy configuration is under control of the relying party, so it is possible to
only accept authenticators for which additional data is available
and meets the requirements.