Abstract
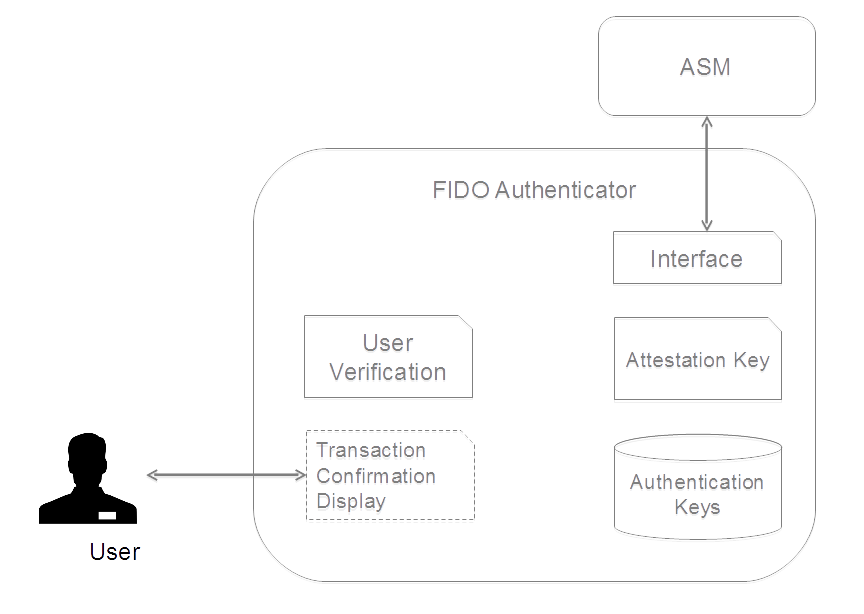
UAF Authenticators may take different forms. Implementations
may range from a secure application running inside
tamper-resistant hardware to software-only solutions on
consumer devices.
This document defines normative aspects of UAF Authenticators and offers security and implementation
guidelines for authenticator implementors.
Status of This Document
This section describes the status of this document at the time of its publication.
Other documents may supersede this document. A list of current FIDO Alliance publications and the
latest revision of this technical report can be found in the FIDO Alliance specifications index at
https://www.fidoalliance.org/specifications/.
This document was published by the FIDO Alliance as a Review Draft.
This document is intended to become a FIDO Alliance Proposed Standard.
If you wish to make comments regarding this document, please
Contact Us.
All comments are welcome.
This is a Review Draft Specification and
is not intended to be a basis for any implementations as the Specification may change. Permission is
hereby granted to use the Specification solely for the purpose of reviewing the Specification. No rights
are granted to prepare derivative works of this Specification. Entities seeking permission to reproduce
portions of this Specification for other uses must contact the FIDO Alliance to determine whether an
appropriate license for such use is available.
Implementation of certain elements of this Specification may require licenses under third party intellectual
property rights, including without limitation, patent rights. The FIDO Alliance, Inc. and its Members
and any other contributors to the Specification are not, and shall not be held, responsible in any manner
for identifying or failing to identify any or all such third party intellectual property rights.
THIS FIDO ALLIANCE SPECIFICATION IS PROVIDED “AS IS” AND WITHOUT ANY
WARRANTY OF ANY KIND, INCLUDING, WITHOUT LIMITATION, ANY EXPRESS OR IMPLIED
WARRANTY OF NON-INFRINGEMENT, MERCHANTABILITY OR FITNESS FOR A
PARTICULAR PURPOSE.
1. Notation
Type names, attribute names and element names are written as
code.
String literals are enclosed in "", e.g. "UAF-TLV".
In formulas we use "|" to denote byte wise concatenation
operations.
UAF specific terminology used in this document is defined in
[FIDOGlossary].
All diagrams, examples, notes in this specification are non-normative.
Unless otherwise specified all data described in this document MUST be encoded in
little-endian format.
All TLV structures can be parsed using a "recursive-descent"
parsing approach. In some cases multiple occurrences of a single tag MAY be allowed
within a structure, in which case all values MUST be
preserved.
All fields in TLV structures are mandatory, unless
explicitly mentioned as otherwise.
This section is normative.
In this document UAF Authenticators use "Tag-Length-Value"
(TLV) format to communicate with the outside world. All
requests and response data MUST be encoded as TLVs.
Commands and existing predefined TLV tags can be extended by
appending other TLV tags (custom or predefined).
Refer to [UAFRegistry] for information about predefined
TLV tags.
TLV formatted data has the following simple structure:
| 2 bytes |
2 bytes |
Length bytes |
| Tag |
Length in bytes |
Data |
All lengths are in bytes. e.g. a UINT32[4] will have
length 16.
Although 2 bytes are allotted for the tag, only
the first 14 bits (values up to 0x3FFF) should be used to
accommodate the limitations of some hardware platforms.
Arrays are implicit. The description of some structures
indicates where multiple values are permitted, and
in these cases, if same tag appears more than once, all values are
signifanct and should be treated as an array.
For convenience in decoding TLV-formatted messages,
all composite tags - those with values that must be parsed by
recursive descent - have the 13th bit (0x1000) set.
A tag that has the 14th bit (0x2000) set indicates that it is
critical and a receiver MUST abort processing
the entire message if it cannot process that tag.
Since UAF Authenticators may have extremely constrained
processing environments, an ASM MUST follow
a normative ordering of structures when sending
commands.
It is assumed that ASM and
Server have sufficient resources to handle parsing
tags in any order so structures send from authenticator MAY use tags in any order.
4.4 Status Codes
| Name |
Value |
Description |
| UAF_CMD_STATUS_OK |
0x00 |
Success. |
| UAF_CMD_STATUS_ERR_UNKNOWN |
0x01 |
An unknown error. |
| UAF_CMD_STATUS_ACCESS_DENIED |
0x02 |
Access to this operation is denied. |
| UAF_CMD_STATUS_USER_NOT_ENROLLED |
0x03 |
User is not enrolled with the authenticator and the
authenticator cannot automatically trigger enrollment.
|
| UAF_CMD_STATUS_CANNOT_RENDER_TRANSACTION_CONTENT |
0x04 |
Transaction content cannot be rendered. |
| UAF_CMD_STATUS_USER_CANCELLED |
0x05 |
User has cancelled the operation. |
| UAF_CMD_STATUS_CMD_NOT_SUPPORTED |
0x06 |
Command not supported. |
| UAF_CMD_STATUS_ATTESTATION_NOT_SUPPORTED |
0x07 |
Required attestation not supported. |
| UAF_CMD_STATUS_PARAMS_INVALID |
0x08 |
The parameters for the command received by the authenticator are malformed/invalid. |
| UAF_CMD_STATUS_KEY_DISAPPEARED_PERMANENTLY |
0x09 |
The UAuth key which is relevant for this command disappeared from
the authenticator and cannot be restored.
On some authenticators this error occurs when the user verification reference data set
was modified (e.g. new fingerprint template added).
|
| UAF_CMD_STATUS_TIMEOUT |
0x0a |
The operation in the authenticator took longer than expected
(due to technical issues)
and it was finally aborted. |
| UAF_CMD_STATUS_USER_NOT_RESPONSIVE |
0x0e |
The user took too long to follow an instruction, e.g. didn't swipe
the finger within the accepted time. |
| UAF_CMD_STATUS_INSUFFICIENT_RESOURCES |
0x0f |
Insufficient resources in the authenticator to perform the requested task. |
| UAF_CMD_STATUS_USER_LOCKOUT |
0x10 |
The operation failed because the user is locked out and the authenticator
cannot automatically trigger an action to change that.
Typically the user would have to enter an alternative
password (formally: undergo some other alternative user verification method) to re-enable the use
of the main user verification method.
Note
Any method the user can use to (re-) enable the main
user verification method is considered an alternative user verification
method and must be properly declared as such. For example, if the user can enter an alternative
password to re-enable the use of fingerprints or to add additional fingers, the authenticator
obviously supports fingerprint or password based user verification.
|
Table 4.4.1: UAF Authenticator Status Codes (0x00 - 0xFF)
5. Structures
This section is normative.
5.1 RawKeyHandle
RawKeyHandle is a structure generated and parsed by the
authenticator. Authenticators MAY define RawKeyHandle in
different ways and the internal structure is relevant only to
the specific authenticator implementation.
RawKeyHandle for a typical first-factor bound authenticator has the following structure.
Depends on hashing
algorithm (e.g. 32 bytes) |
Depends on key type.
(e.g. 32 bytes) |
Username Size
(1 byte) |
Max 128 bytes |
| KHAccessToken |
UAuth.priv |
Size |
Username |
Table 5.1: RawKeyHandle Structure
First Factor authenticators MUST store Usernames in the authenticator
and they MUST link the Username to the related key. This MAY be achieved by storing
the Username inside the RawKeyHandle.
Second Factor authenticators MUST NOT store the Username.
The ability to support Usernames is a key difference between first-, and
second-factor authenticators.
The RawKeyHandle MUST be cryptographically wrapped before leaving the
authenticator boundary since it typically contains sensitive information, e.g.
the user authentication private key (UAuth.priv).
5.2 Structures to be parsed by FIDO Server
The structures defined in this section are created by UAF Authenticators
and parsed by FIDO Servers.
Authenticators MUST generate these structures if they implement "UAFV1TLV" assertion scheme.
Note
"UAFV1TLV" assertion scheme assumes that the authenticator has
exclusive control over all data included inside TAG_UAFV1_KRD and TAG_UAFV1_SIGNED_DATA.
The nesting structure
MUST be preserved, but the order of tags within
a composite tag is not normative. FIDO Servers
MUST be prepared to handle tags appearing in any
order.
5.2.1 TAG_UAFV1_REG_ASSERTION
The following TLV structure is generated by the
authenticator during processing of a Register command. It
is then delivered to FIDO Server intact, and parsed by the
server. The structure embeds a TAG_UAFV1_KRD tag which
among other data contains the newly generated UAuth.pub.
If the authenticator wants to append custom
data to TAG_UAFV1_KRD structure (and thus sign with
Attestation Key) - this data MUST be included as
TAG_EXTENSION_DATA in a TAG_EXTENSION object inside TAG_UAFV1_KRD.
If the authenticator wants to send additional data to
FIDO Server without signing it - this data MUST be included
as TAG_EXTENSION_DATA in a TAG_EXTENSION object
inside TAG_UAFV1_REG_ASSERTION and not inside TAG_UAFV1_KRD.
Currently this document only specifies
TAG_ATTESTATION_BASIC_FULL, TAG_ATTESTATION_BASIC_SURROGATE and TAG_ATTESTATION_ECDAA.
In case if the authenticator is required to perform "Some_Other_Attestation" on
TAG_UAFV1_KRD - it MUST use the TLV tag and content defined for
"Some_Other_Attestation" (defined in [UAFRegistry]).
|
TLV Structure |
Description |
| 1 |
UINT16 Tag |
TAG_UAFV1_REG_ASSERTION |
| 1.1 |
UINT16 Length |
Length of the structure |
| 1.2 |
UINT16 Tag |
TAG_UAFV1_KRD |
| 1.2.1 |
UINT16 Length |
Length of the structure |
| 1.2.2 |
UINT16 Tag |
TAG_AAID |
| 1.2.2.1 |
UINT16 Length |
Length of AAID |
| 1.2.2.2 |
UINT8[] AAID |
Authenticator Attestation ID |
| 1.2.3 |
UINT16 Tag |
TAG_ASSERTION_INFO |
| 1.2.3.1 |
UINT16 Length |
Length of Assertion Information |
| 1.2.3.2 |
UINT16 AuthenticatorVersion |
Vendor assigned authenticator version |
| 1.2.3.3 |
UINT8 AuthenticationMode |
For Registration this must be 0x01 indicating
that the user has explicitly verified the action. |
| 1.2.3.4 |
UINT16 SignatureAlgAndEncoding |
Signature Algorithm and Encoding of the attestation signature.
Refer to [FIDORegistry] for information on
supported algorithms and their values.
|
| 1.2.3.5 |
UINT16 PublicKeyAlgAndEncoding |
Public Key algorithm and encoding of the newly generated UAuth.pub key.
Refer to [FIDORegistry] for information on
supported algorithms and their values.
|
| 1.2.4 |
UINT16 Tag |
TAG_FINAL_CHALLENGE_HASH |
| 1.2.4.1 |
UINT16 Length |
Final Challenge Hash length |
| 1.2.4.2 |
UINT8[] FinalChallengeHash |
(binary value of) Final Challenge Hash provided in the
Command |
| 1.2.5 |
UINT16 Tag |
TAG_KEYID |
| 1.2.5.1 |
UINT16 Length |
Length of KeyID |
| 1.2.5.2 |
UINT8[] KeyID |
(binary value of) KeyID for the key generated by
the Authenticator |
| 1.2.6 |
UINT16 Tag |
TAG_COUNTERS |
| 1.2.6.1 |
UINT16 Length |
Length of Counters |
| 1.2.6.2 |
UINT32 SignCounter |
Signature Counter.
Indicates how many times this authenticator has
performed signatures in the past.
|
| 1.2.6.3 |
UINT32 RegCounter |
Registration Counter.
Indicates how many times this authenticator has
performed registrations in the past.
|
| 1.2.7 |
UINT16 Tag |
TAG_PUB_KEY |
| 1.2.7.1 |
UINT16 Length |
Length of UAuth.pub |
| 1.2.7.2 |
UINT8[] PublicKey |
User authentication public key (UAuth.pub) newly
generated by authenticator |
| 1.3 (choice 1) |
UINT16 Tag |
TAG_ATTESTATION_BASIC_FULL |
| 1.3.1 |
UINT16 Length |
Length of structure |
| 1.3.2 |
UINT16 Tag |
TAG_SIGNATURE |
| 1.3.2.1 |
UINT16 Length |
Length of signature |
| 1.3.2.2 |
UINT8[] Signature |
Signature calculated with Basic Attestation Private
Key over TAG_UAFV1_KRD content.
The entire TAG_UAFV1_KRD content,
including the tag and it's length field, MUST be
included during signature computation.
|
| 1.3.3 |
UINT16 Tag |
TAG_ATTESTATION_CERT (multiple occurrences possible)
Multiple occurrences must be ordered. The attestation certificate MUST occur first.
Each subsequent occurrence (if exists) MUST be the issuing certificate of
the previous occurrence.
The last occurence MUST be chained to one of the certificates included
in field attestationRootCertificate in
the related Metadata Statement [FIDOMetadataStatement].
|
| 1.3.3.1 |
UINT16 Length |
Length of Attestation Cert |
| 1.3.3.2 |
UINT8[] Certificate |
Single X.509 DER-encoded [ITU-X690-2008] Attestation Certificate or a single certificate
from the attestation certificate chain (see description above).
|
| 1.3 (choice 2) |
UINT16 Tag |
TAG_ATTESTATION_BASIC_SURROGATE |
| 1.3.1 |
UINT16 Length |
Length of structure |
| 1.3.2 |
UINT16 Tag |
TAG_SIGNATURE |
| 1.3.2.1 |
UINT16 Length |
Length of signature |
| 1.3.2.2 |
UINT8[] Signature |
Signature calculated with newly generated UAuth.priv key over TAG_UAFV1_KRD content.
The entire TAG_UAFV1_KRD content,
including the tag and it's length field, MUST be
included during signature computation.
|
| 1.3 (choice 3) |
UINT16 Tag |
TAG_ATTESTATION_ECDAA |
| 1.3.1 |
UINT16 Length |
Length of structure |
| 1.3.2 |
UINT16 Tag |
TAG_SIGNATURE |
| 1.3.2.1 |
UINT16 Length |
Length of signature |
| 1.3.2.2 |
UINT8[] Signature |
The binary ECDAA signature as specified in [FIDOEcdaaAlgorithm].
|
5.2.2 TAG_UAFV1_AUTH_ASSERTION
The following TLV structure is generated by an
authenticator during processing of a Sign command. It is
then delivered to FIDO Server intact and parsed by the
server. The structure embeds a TAG_UAFV1_SIGNED_DATA tag.
If the authenticator wants to append custom
data to TAG_UAFV1_SIGNED_DATA structure (and thus sign with
Attestation Key) - this data MUST be included as an
additional tag inside TAG_UAFV1_SIGNED_DATA.
If the authenticator wants to send additional data to
FIDO Server without signing it - this data MUST be included
as an additional tag inside TAG_UAFV1_AUTH_ASSERTION and not inside TAG_UAFV1_SIGNED_DATA.
|
TLV Structure |
Description |
| 1 |
UINT16 Tag |
TAG_UAFV1_AUTH_ASSERTION |
| 1.1 |
UINT16 Length |
Length of the structure. |
| 1.2 |
UINT16 Tag |
TAG_UAFV1_SIGNED_DATA |
| 1.2.1 |
UINT16 Length |
Length of the structure. |
| 1.2.2 |
UINT16 Tag |
TAG_AAID |
| 1.2.2.1 |
UINT16 Length |
Length of AAID |
| 1.2.2.2 |
UINT8[] AAID |
Authenticator Attestation ID |
| 1.2.3 |
UINT16 Tag |
TAG_ASSERTION_INFO |
| 1.2.3.1 |
UINT16 Length |
Length of Assertion Information |
| 1.2.3.2 |
UINT16 AuthenticatorVersion |
Vendor assigned authenticator version. |
| 1.2.3.3 |
UINT8 AuthenticationMode |
Authentication Mode indicating whether user
explicitly verified or not and indicating if there
is a transaction content or not.
- 0x01 means that user has been explicitly
verified
- 0x02 means that transaction content has been
shown on the display and user confirmed it by
explicitly verifying with authenticator
|
| 1.2.3.4 |
UINT16 SignatureAlgAndEncoding |
Signature algorithm and encoding format.
Refer to [FIDORegistry] for information on
supported algorithms and their values.
|
| 1.2.4 |
UINT16 Tag |
TAG_AUTHENTICATOR_NONCE |
| 1.2.4.1 |
UINT16 Length |
Length of authenticator Nonce - MUST be at least 8
bytes, and NOT longer than 64 bytes. |
| 1.2.4.2 |
UINT8[] AuthnrNonce |
(binary value of) A nonce randomly generated by
Authenticator |
| 1.2.5 |
UINT16 Tag |
TAG_FINAL_CHALLENGE_HASH |
| 1.2.5.1 |
UINT16 Length |
Length of Final Challenge Hash |
| 1.2.5.2 |
UINT8[] FinalChallengeHash |
(binary value of) Final Challenge Hash provided in the
Command |
| 1.2.6 |
UINT16 Tag |
TAG_TRANSACTION_CONTENT_HASH |
| 1.2.6.1 |
UINT16 Length |
Length of Transaction Content Hash. This length is 0 if
AuthenticationMode == 0x01, i.e. authentication, not transaction confirmation. |
| 1.2.6.2 |
UINT8[] TCHash |
(binary value of) Transaction Content Hash |
| 1.2.7 |
UINT16 Tag |
TAG_KEYID |
| 1.2.7.1 |
UINT16 Length |
Length of KeyID |
| 1.2.7.2 |
UINT8[] KeyID |
(binary value of) KeyID |
| 1.2.8 |
UINT16 Tag |
TAG_COUNTERS |
| 1.2.8.1 |
UINT16 Length |
Length of Counters |
| 1.2.8.2 |
UINT32 SignCounter |
Signature Counter.
Indicates how many times this authenticator has
performed signatures in the past.
|
| 1.3 |
UINT16 Tag |
TAG_SIGNATURE |
| 1.3.1 |
UINT16 Length |
Length of Signature |
| 1.3.2 |
UINT8[] Signature |
Signature calculated using UAuth.priv over
TAG_UAFV1_SIGNED_DATA structure.
The entire TAG_UAFV1_SIGNED_DATA content,
including the tag and it's length field, MUST be
included during signature computation.
|
5.3 UserVerificationToken
This specification doesn't specify how exactly user verification must be performed
inside the authenticator. Verification is considered to be an authenticator, and vendor, specific operation.
This document provides an example on how the "vendor_specific_UserVerify" command (a command which
verifies the user using Authenticator's built-in technology) could be securely bound to
UAF Register and Sign commands. This binding is done through a concept called UserVerificationToken.
Such a binding allows decoupling "vendor_specific_UserVerify" and "UAF Register/Sign" commands
from each other.
Here is how it is defined:
-
The ASM invokes the "vendor_specific_UserVerify" command.
The authenticator verifies the user and returns a
UserVerificationToken back.
-
The ASM invokes UAF.Register/Sign command and passes
UserVerificationToken to it.
The authenticator verifies the validity of UserVerificationToken and
performs the FIDO operation if it is valid.
The concept of UserVerificationToken is non-normative. An authenticator might decide to implement this
binding in a very different way.
For example an authenticator vendor may decide to append a UAF Register request directly to their
"vendor_specific_UserVerify" command and process both as a single command.
If UserVerificationToken binding is implemented, it should either meet one of the
following criteria or implement a mechanism providing similar, or better security:
-
UserVerificationToken must allow performing only a single UAF Register or UAF Sign operation.
-
UserVerificationToken must be time bound, and allow performing multiple UAF operations
within the specified time.
8. Access Control for Commands
This section is normative.
FIDO Authenticators MAY implement various mechanisms to
guard access to privileged commands.
The following table summarizes the access control
requirements for each command.
All UAF Authenticators MUST satisfy the access control
requirements defined below.
Authenticator vendors MAY offer additional security
mechanisms.
Terms used in the table:
- NoAuth - no access control
- UserVerify - explicit user verification
- KHAccessToken - MUST be known to the caller
(or alternative method with similar security level MUST be used)
- KeyHandleList - MUST be known to the caller
- KeyID - MUST be known to the caller
| Command |
First-factor Bound Authenticator |
2ndF Bound Authenticator |
First-factor Roaming Authenticator |
2ndF Roaming Authenticator |
| GetInfo |
NoAuth |
NoAuth |
NoAuth |
NoAuth |
| OpenSettings |
NoAuth |
NoAuth |
NoAuth |
NoAuth |
| Register |
UserVerify |
UserVerify |
UserVerify |
UserVerify |
| Sign |
UserVerify
KHAccessToken
KeyHandleList
|
UserVerify
KHAccessToken
KeyHandleList
|
UserVerify
KHAccessToken |
UserVerify
KHAccessToken
KeyHandleList
|
| Deregister |
KHAccessToken
KeyID |
KHAccessToken
KeyID |
KHAccessToken
KeyID |
KHAccessToken
KeyID |
Table 1: Access Control for Commands